Peace of mind, all the time
The software development life cycle is continuous. Traditional cybersecurity tools are not. We help you integrate security monitoring into your SDLC.
Bake security into your code
Software sits at the center of digital transformation. Minimizing the risk in code is a must to stay ahead of threats.
Secure apps start with secure code
Secure software build cycles tailored to your API requirements ensure every deployment is tightly integrated with your existing business workflows.
Secure software build cycles tailored to your API requirements ensure every deployment is tightly integrated with your existing business workflows.
Match security to your growth
Your application stack’s security is only as strong as your ability to respond quickly to emerging vulnerabilities.
Your application stack’s security is only as strong as your ability to respond quickly to emerging vulnerabilities.
Corner the market, cover your risks
Your customers rely on your applications to deliver well-tailored, unique experiences – not to put them at risk. Cover yourself and your customers with proactive security.
Your customers rely on your applications to deliver well-tailored, unique experiences – not to put them at risk. Cover yourself and your customers with proactive security.

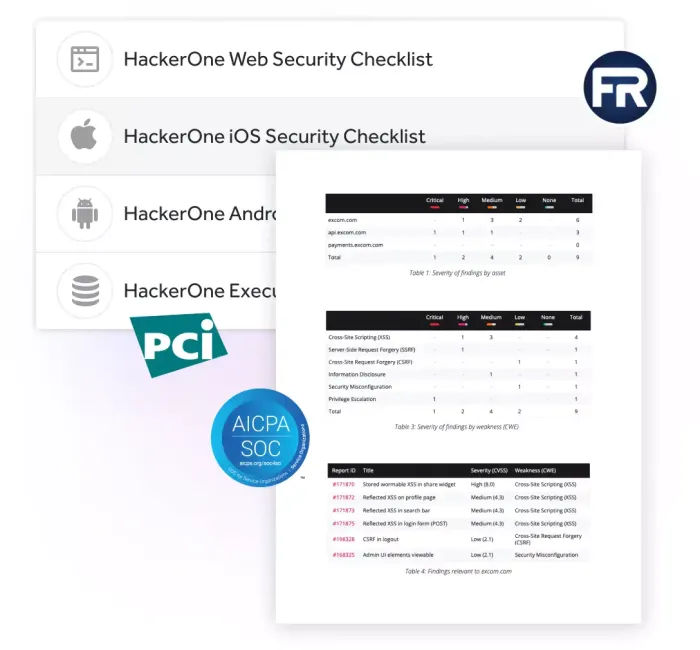
Know the risk, make the fix, anytime.
Unified analytics show you the vulnerabilities that pose the greatest threat, and plot your path to remediation.
- Improve and scale software delivery with continuous security testing.
- Engage security experts to help agile teams identify and fix vulnerabilities before they become breaches.
- Launch new applications with confidence, knowing talented hackers have vetted your code.
Compliance checks that won’t slow your pipeline.
As attack surfaces expand, organizations need to rapidly validate their risk profile to assure business continuity, comply with mandates and deliver trusted experiences to customers.
- Quickly meet compliance and regulatory standards to assure your product launches stay on track.
- Measure threats, examine the landscape, and demonstrate value to stakeholders, customers, and partners.