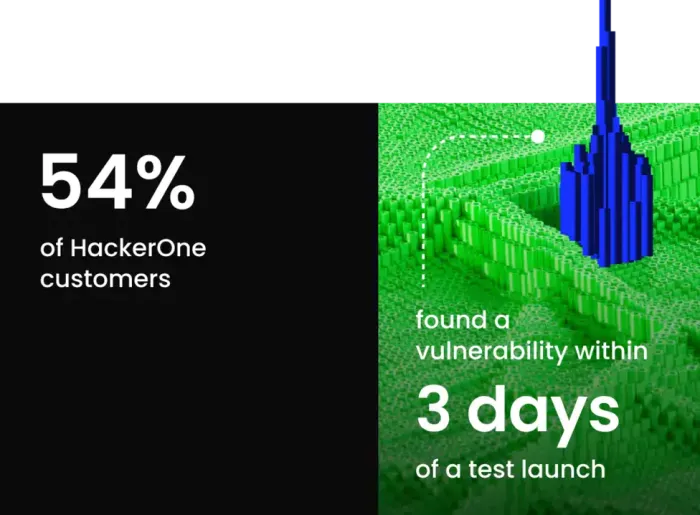
Move beyond point-in-time security
Combine the ingenuity of human security experts with real-time attack surface insight to achieve continuous testing of your evolving digital landscape.
Adversarial security to outsmart cybercriminals
Engage an elite community of ethical hackers to test your applications from an adversarial point of view—finding highly exploitable vulnerabilities before cybercriminals do.
Keep pace with new deployments.
Remove SDLC blockers that come from point-in-time security testing as a release gate.
Remove SDLC blockers that come from point-in-time security testing as a release gate.
Prioritize the biggest risks.
Allocate limited resources efficiently by tackling the riskiest issues first, and demonstrate immediate ROI.
Allocate limited resources efficiently by tackling the riskiest issues first, and demonstrate immediate ROI.
Scale security capabilities.
Remove SDLC blockers that come from point-in-time security testing as a release gate.
Remove SDLC blockers that come from point-in-time security testing as a release gate.
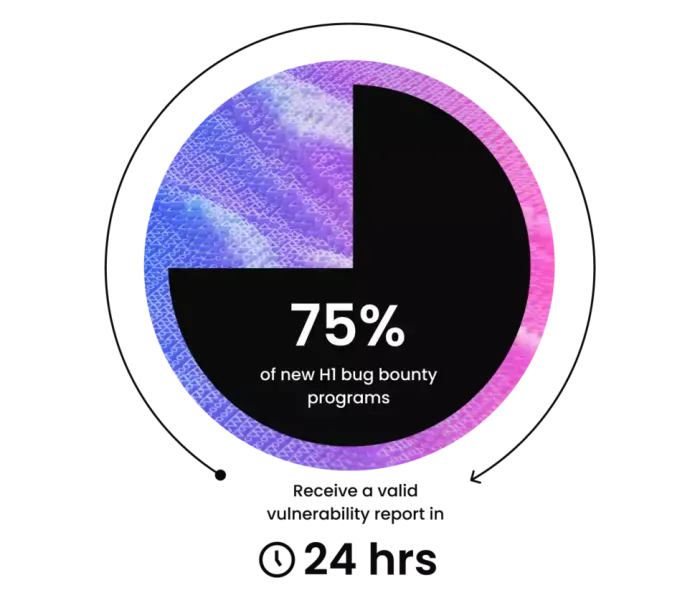
On-demand pentests
Validate security coverage with Pentest as a Service (PTaaS). You’ll get direct access to an extensive pool of vetted expert testers—and receive findings in real time to fix vulnerabilities fast.
Spotlight on business-critical applications
Provide incentives for ethical hackers to pinpoint flaws in mission-critical digital assets, find zero days, and release secure-by-design new products. Plus, reduce mean time to repair (MTTR) by prioritizing risks for security teams.