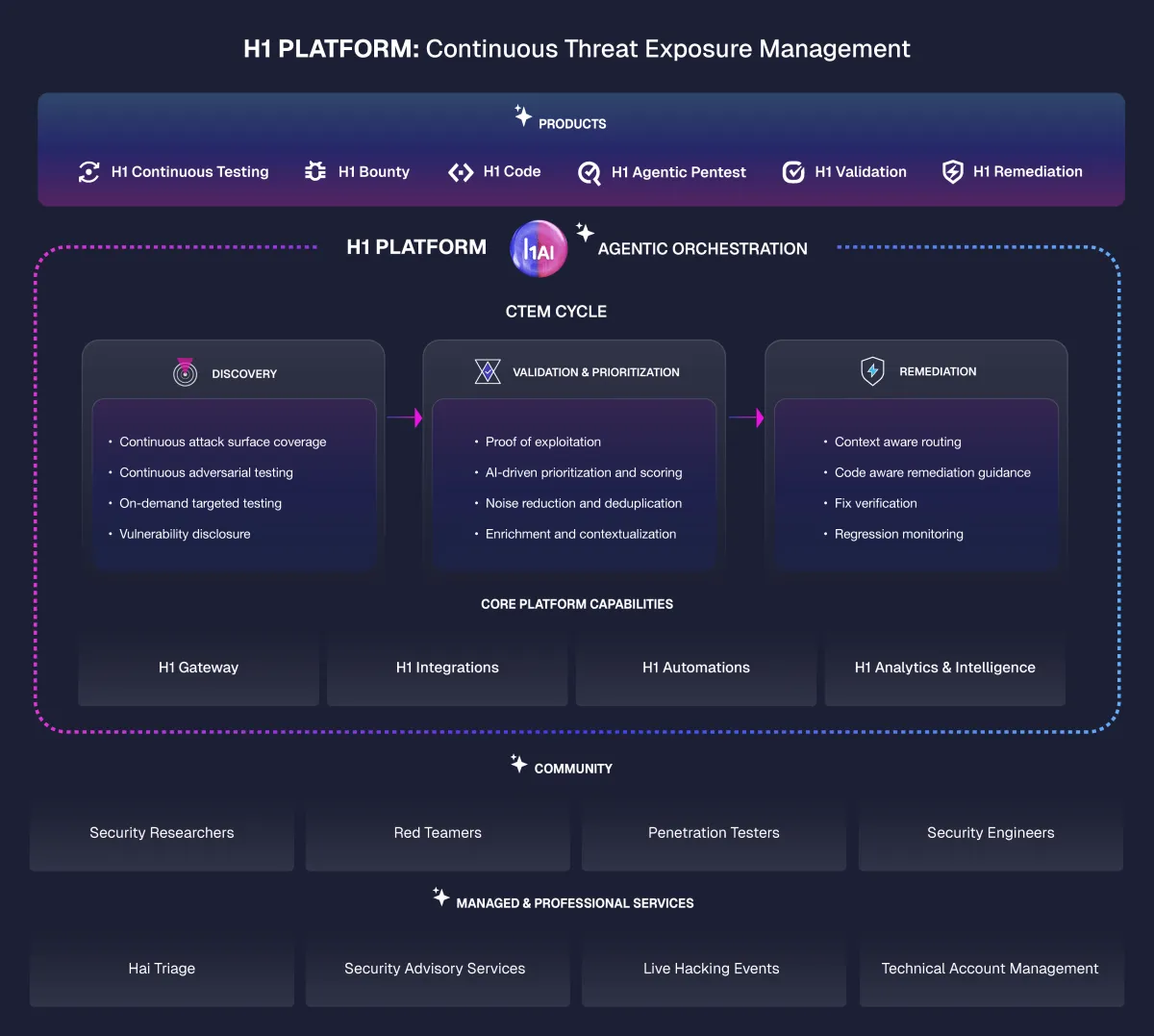
Eliminate Exploitable Risk
The agentic H1 Platform continuously discovers, validates, prioritizes, and remediates exploitable risk across your entire attack surface, at the speed and accuracy the current threat environment demands.
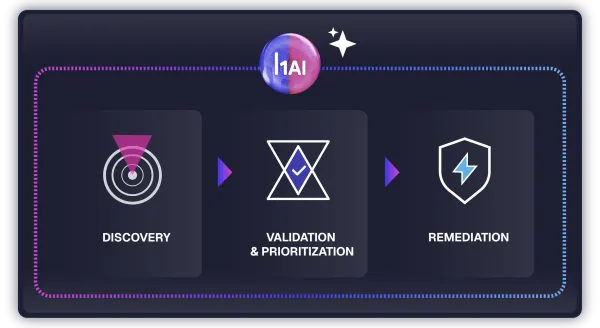
Hai powers every stage.
Hai, our agentic AI orchestrator, coordinates agents across every stage of the platform as a single connected system. It scores and validates findings continuously, routes confirmed exposures to the right owner, and gets more accurate the longer it runs.
Discovery
Continuous coverage across your full attack surface.
- Always-on agentic testing across your full attack surface to surface confirmed, exploitable findings
- New exposures and regressions are caught as they emerge, unifying findings from H1-native solutions and third-party sources
Validation & Prioritization
Confirm what's exploitable, act on what matters.
- Hai scores every incoming finding, eliminates noise, and surfaces what is actually exploitable in your environment
- The validation pipeline handles thousands of reports per week at 95% accuracy, improving signal by 40%
Remediation
Close the loop from exploitable finding to verified fix.
- Developer-ready remediation guidance routes each finding to the right owner with full exploit context, delivered into the tools your team already uses
- Retests confirm fixes hold and regression monitoring catches recurrences before they reopen
Core Platform Capabilities
Connecting and amplifying every stage of the find-to-fix loop.
- Continuous asset discovery and exposure scoring, workflow automation, and 36+ integrations
- Cross-program dashboards track exposure velocity, remediation speed, and signal quality
- Self-serve Return on Mitigation delivers a board-ready measure of avoided financial loss
Community
Adversarial creativity with AI, to find what no training set contains.
- An elite researcher community operates at the adversarial frontier, finding what no automated system reaches alone
- Surface business logic flaws, novel attack chains, and techniques no training set contains
Managed and Professional Services
AI-powered expertise with human-led outcomes.
- Expert services extend the platform at every stage, helping your program reach full operational maturity faster
- Whether you're building from scratch or scaling an existing program, our team accelerates time to value
Find, validate, and fix what matters with the right product for every stage.
Start where you have the most friction. Each product is an entry point into the full H1 Platform, purpose-built for your needs and ready to scale as your needs evolve.