Humans find what automation can’t.
Put the world’s largest community of ethical hackers to work for you.
5 keys to effective human-powered security
2 million security experts at the ready
HackerOne matches you with thoroughly vetted, top-notch security talent from our global community of 2M+ hackers. 91% of HackerOne customers say hackers provide more impactful and valuable vulnerability reports than AI or scanning solutions.
Everything you need to eliminate unknown risk
Seamlessly manage pentests, bug bounties, vulnerability disclosure, and code review in one place—fulfilling your evolving needs for continuous, preemptive security testing.
Tailoring programs to your goals & requirements
We start by gaining a deep understanding of your security goals and challenges, then work with you to design a program that meets your needs. Our ultimate aim is to help you maximize your programs’ ROI and measurably reduce your risk.

All signal, no noise
We go beyond simple SLA-based intake—validating each vulnerability's legitimacy, severity, and impact. The result: a customer satisfaction score of 4.71 out of 5.

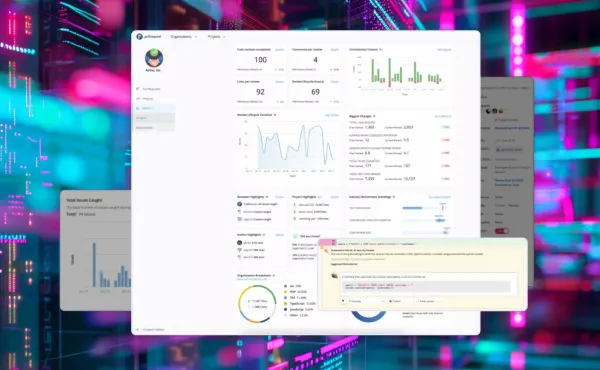
Optimizing your program & your teams’ time
Track key metrics like response times, report submissions, rewards paid, and remediation statuses in real time. Leverage our vast dataset and proprietary AI to benchmark your program against industry peers and forecast trends.

How can human-powered security help you?
Growing attack surfaces.
Rapid AI proliferation. Faster SDLCs than ever before. The devastating cost of a breach. The security skills shortage.
Traditional security tools and methods are no longer sufficient to keep you ahead of cybercrime. But a vast global community of ethical hackers can work 24x7 to uncover hidden weaknesses in your systems before bad actors do.
Rapid AI proliferation. Faster SDLCs than ever before. The devastating cost of a breach. The security skills shortage.
Traditional security tools and methods are no longer sufficient to keep you ahead of cybercrime. But a vast global community of ethical hackers can work 24x7 to uncover hidden weaknesses in your systems before bad actors do.
$4.88M vs. $4.2k
The average cost of a data breach exceeds $4.45 million. 2 The average bug bounty paid to a hacker for a high- or critical-severity vulnerability is just $3,700. Human–powered security can pay for itself with just a single vulnerability report.
The average cost of a data breach exceeds $4.45 million. 2 The average bug bounty paid to a hacker for a high- or critical-severity vulnerability is just $3,700. Human–powered security can pay for itself with just a single vulnerability report.
70%
of HackerOne customers say hacker efforts have helped them avoid a significant security incident1
of HackerOne customers say hacker efforts have helped them avoid a significant security incident1
10%
of security researchers now specialize in hacking on AI models and deployments as AI assets in scope for bug bounty programs has increased by 171% in 2024.
of security researchers now specialize in hacking on AI models and deployments as AI assets in scope for bug bounty programs has increased by 171% in 2024.
How it works
1
Define your scope
Easily manage your program's scope from a single interface. Select the assets you want tested, such as web domains or mobile apps, and add them to active tests.
Define your scope
Easily manage your program's scope from a single interface. Select the assets you want tested, such as web domains or mobile apps, and add them to active tests.
2
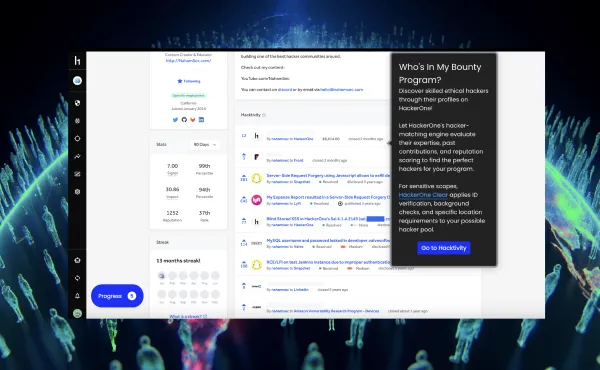
Connect with hackers
Our intelligent matching technology connects you with security researchers who have the skills and experience needed for your program. Communicate with individual hackers or groups directly in the HackerOne platform.
Connect with hackers
Our intelligent matching technology connects you with security researchers who have the skills and experience needed for your program. Communicate with individual hackers or groups directly in the HackerOne platform.
3
Discover & triage
As vulnerabilities roll in, HackerOne's triage services ensure you see only valid, prioritized reports. Our team of 40+ security analysts across 5 continents handles over 200,000 reports yearly so you can focus on the most critical issues.
Discover & triage
As vulnerabilities roll in, HackerOne's triage services ensure you see only valid, prioritized reports. Our team of 40+ security analysts across 5 continents handles over 200,000 reports yearly so you can focus on the most critical issues.
4
Reward
Strengthen your relationships with researchers by rewarding them for their contributions. Send payments, swag, or other rewards through the HackerOne platform.
Reward
Strengthen your relationships with researchers by rewarding them for their contributions. Send payments, swag, or other rewards through the HackerOne platform.
5
Remediate
HackerOne provides remediation advice for each vulnerability, so your development and security teams can quickly understand and resolve the issue. And you can use Hai, our AI copilot, to enrich vulnerability reports with context and recommendations to speed up your find-to-fix cycles.
Remediate
HackerOne provides remediation advice for each vulnerability, so your development and security teams can quickly understand and resolve the issue. And you can use Hai, our AI copilot, to enrich vulnerability reports with context and recommendations to speed up your find-to-fix cycles.
6
Improve continuously
Feed insights from your programs back into your SDLC to enable continuous improvement—helping development teams build more secure products from the ground up.
Improve continuously
Feed insights from your programs back into your SDLC to enable continuous improvement—helping development teams build more secure products from the ground up.










