HackerOne’s 2026 research shows AI adoption is outpacing security testing. Continuous security testing with seven methods helps CISOs close the coverage gap.
HackerOne Blog
The latest from HackerOne
Image
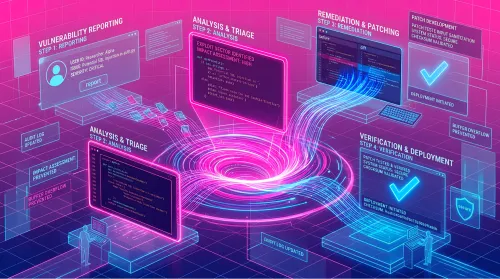
AI is making vulnerability discovery cheap. CTEM only reduces risk when teams validate exploitability, remediate, and retest to prove fixes hold.