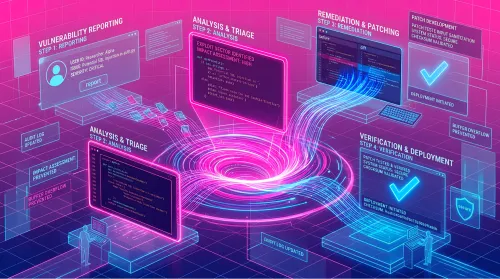
A 100%+ surge in AI-assisted bug bounty submissions changed how HackerOne thinks about quality, triage, and researcher accountability. Here's what we learned navigating the wave and how we're building for what's next.
HackerOne Blog
The latest from HackerOne
Image

Vulnerability submissions are up 76%. Unresolved criticals grew 25x. HackerOne platform data reveals a widening remediation gap that security teams can't afford to ignore.