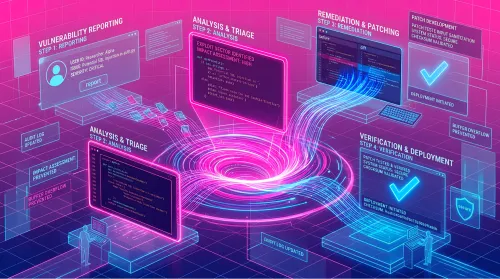
We benchmarked Claude Opus 4.7 on code-backed vulnerability validation. See accuracy gains, fewer false positives, and what it means for triage.
HackerOne Blog
Exposure Management
Image

Security leaders forecast 2026 as the year CTEM becomes essential, with AI-driven threats, agentic security, and continuous validation reshaping cyber risk.