New Security Inbox & Dashboard

At HackerOne, we're on a mission to empower the world to build a safer internet. Better security begins with a quality vulnerability coordination process, and our free platform enables your team to seamlessly manage the entire workflow. Think of it as a replacement for your old shared security inbox.
Since our launch in early 2013, we've enabled nearly 100 organizations to work with security researchers to safely resolve over 3,500 bugs, awarding over one million dollars in bounties in the process! Over the past month, we've been rolling out some great new features that make the vulnerability coordination process even easier.
New Security Inbox
We've redesigned the HackerOne interface to enable faster and more efficient bug processing. With this new, intuitive layout, you can navigate through your entire list of bugs on the left side of the screen, with each bug's details opening in a pane on the right. As a result, individual reports now open inline, which means no more clicking forward and backward to navigate between bugs! This interface was also designed to take advantage of all of your screen space, especially if you have a larger display.
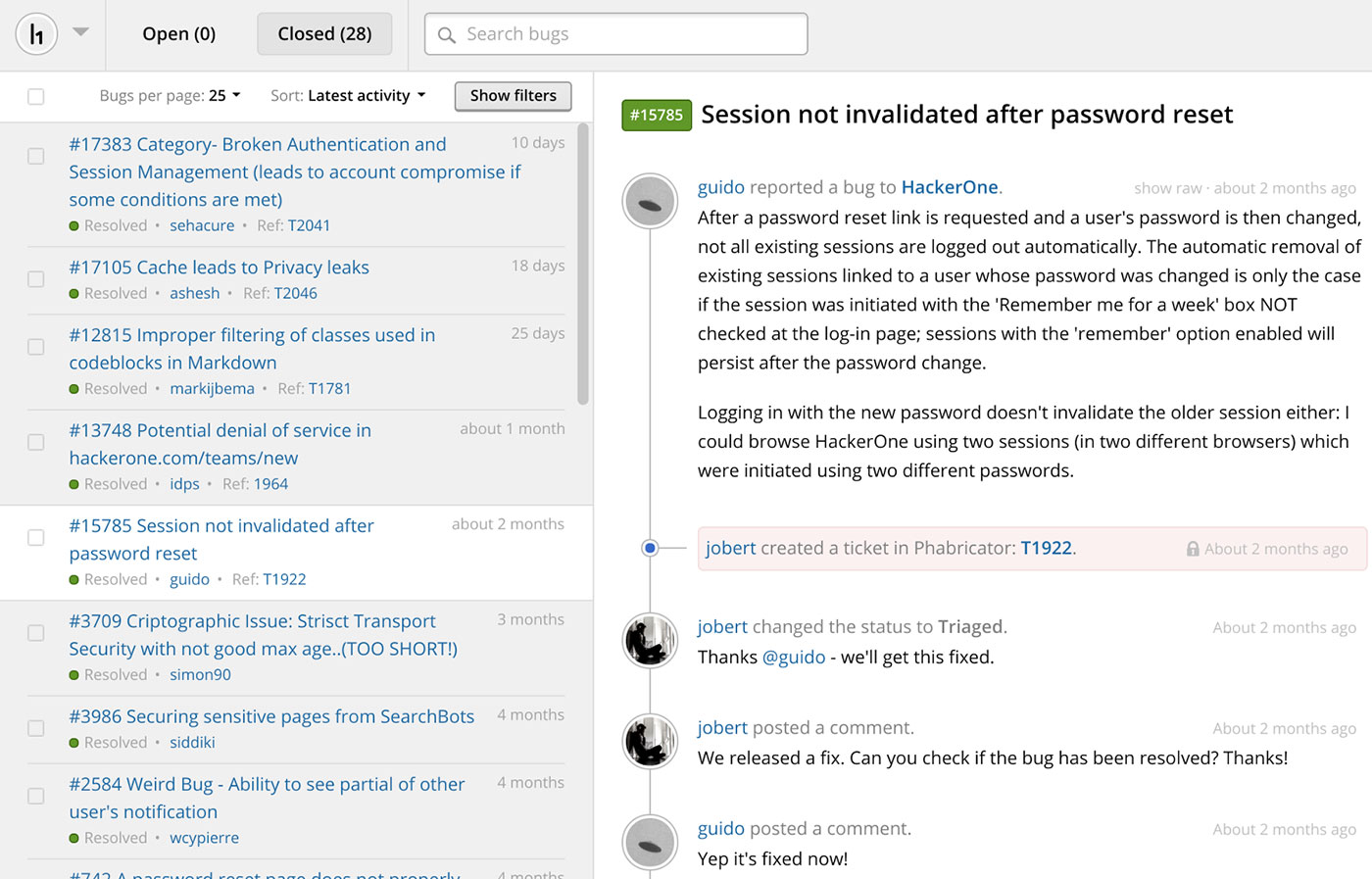
Search
We're also rolling out one of the features that you've requested most frequently: search. Filtering search allows you to quickly target the bug you're looking for, without having to scroll or remember the last time you engaged with it, saving you time and energy.
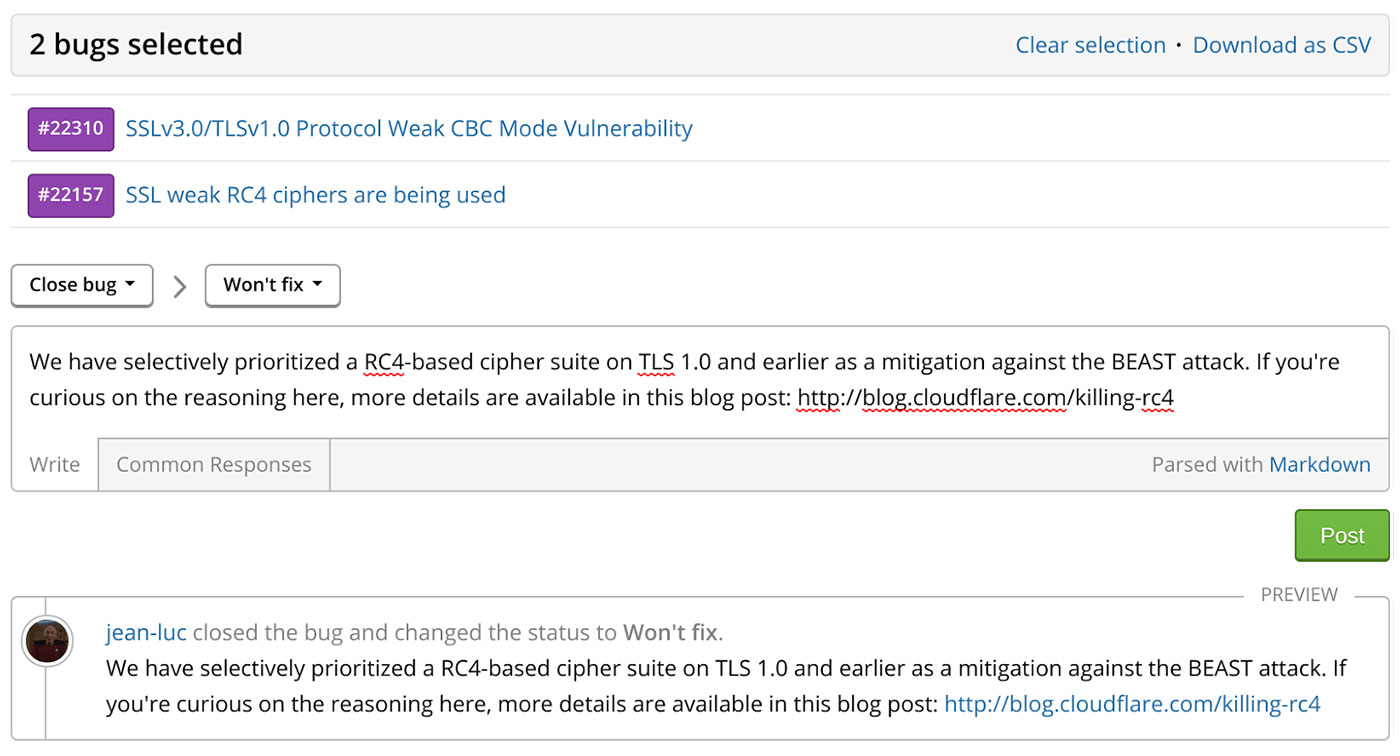
Bulk Actions
Bulk actions are even easier in the new interface with support for applying the same action to multiple reports with a single click. Combine it with search and filters to save even more time.
A couple of scenarios in which this could come in handy are:
- Assigning a batch of reports to a team member
- Closing a series of related reports based on a search criteria
- Merging duplicate reports of the same underlying issue
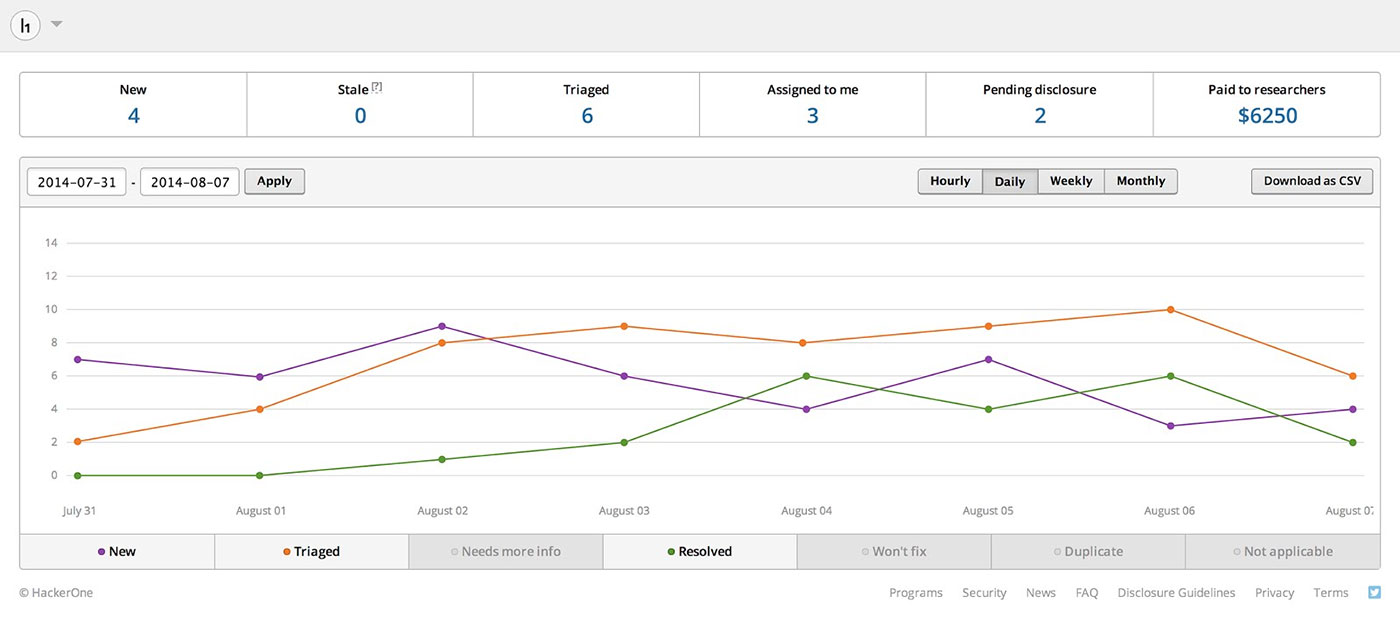
Insights Dashboard
Our brand new Dashboard enables unparalleled insight into your security response posture with metrics gleaned from around-the-clock security assessments. Monitor your team's stats in real-time to effortlessly stay on top of response time, stale issues, pending disclosures, and more. This is a powerful way to stay up to date with your team's status at a glance and proactively identify potential areas in need of attention.
Keyboard Shortcuts
To improve the speed and efficiency of your workflow, we've added several keyboard shortcuts for even faster navigation. We'll be adding more soon, so stay tuned!
Integration, Communication, and Automation
These efficiency-enhancing features have been built in to the HackerOne platform for a while, but are worth mentioning here:
- Integrates directly with your existing internal bug tracking system - No cutting and pasting from email or other report formats to file a bug with your internal teams! We currently support many popular bug tracking systems (JIRA, Bugzilla, Phabricator, and more). If we don't support yours, we'll build support for it.
- Customizable Common Responses - We have several common responses we've built in to the platform to help your response team get up and running as efficiently as possible. Add your own that map to your common scenarios.
- Automated response triggers - Don't Repeat Yourself. You've got better things to do than respond to another known false positive. We give you the ability to create custom triggers to deal with certain bugs automatically, freeing your response team to focus on the most critical reports.
Our goal is to make the vulnerability coordination process as efficient and smooth as possible, and we believe that these features are another big step in that direction, whether you offer a bug bounty or not. We hope they make your life easier. Let us know what you'd like to see us build next.
HackerOne is the #1 hacker-powered security platform, helping organizations find and fix critical vulnerabilities before they can be criminally exploited. As the contemporary alternative to traditional penetration testing, our bug bounty program solutions encompass vulnerability assessment, crowdsourced testing and responsible disclosure management. Discover more about our security testing solutions or Contact Us today.


