Disclosure Assistance Refresh

Ever stumbled upon a vulnerability, but had no idea how to share it with the affected organization? You DM them on Twitter, email their support alias, but aren’t able to get a hold of them? HackerOne can help! We’ve blogged about “Disclosure Assistance” before, but we wanted to talk about it again, as there have been some changes.
Let’s review how Disclosure Assistance works:
- Hacker finds a vulnerability in XYZ Company
- Hacker tries to report the vulnerability to XYZ Company, but can’t figure out how, or attempts to contact them have failed
- Hacker looks up XYZ Company in the HackerOne Directory
- Hacker clicks on “Disclosure Assistance”
- NEW! A form pops up where the hacker can provide context around the request to help HackerOne triage it. This form asks the hacker whether they’ve tried to contact the company, what type of vulnerability it is, and the affected domain/IP/URL.
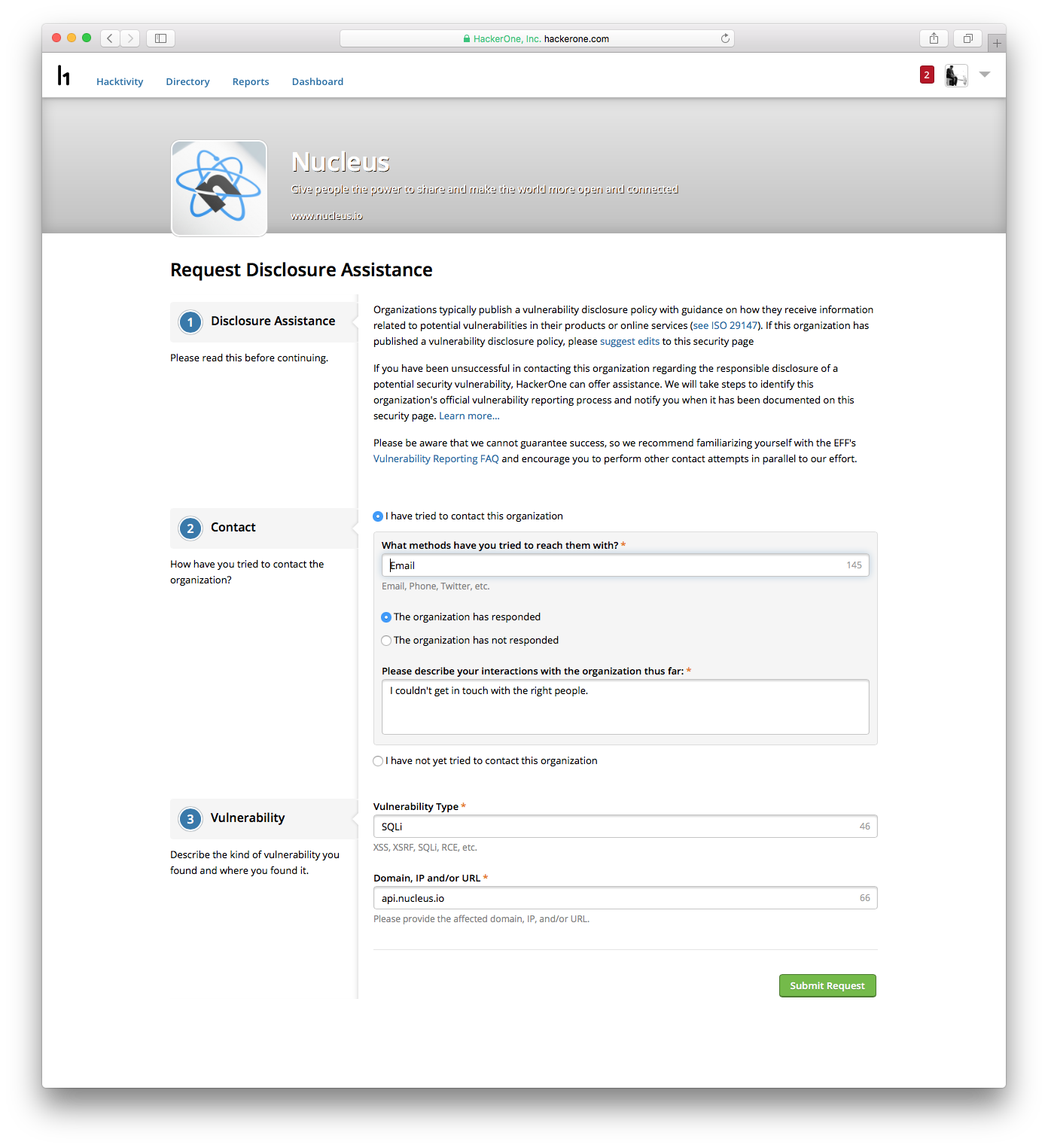 NEW Disclosure Assistance Context Form
NEW Disclosure Assistance Context Form
At this point, HackerOne reviews the requests that have come in. Please note that we cannot respond to every Disclosure Assistance request, but we will make our best effort to get you in touch with the affected organization. If you’ve submitted a Disclosure Assistance request in the past and have not received a response, feel free to submit it again with the new context form - this will help us have more information to work with!
A few quick reminders on Disclosure Assistance:
- HackerOne cannot and does not condone hacking on any organization without their permission.
- HackerOne does not ask hackers for specific vulnerability details, we only try to connect friendly hackers with the affected organizations to facilitate a discussion to ensure the issue can be responsibly disclosed. As such, HackerOne can’t always verify the legitimacy of the vulnerability, and we’ll tend to prioritize requests from hackers with higher signal.
- HackerOne cannot guarantee success - we will try our best to make a connection between the hacker and the affected organization, but it’s important to keep the EFF’s Vulnerability Reporting FAQ in mind throughout this process.
That’s it! Please see our original blog post on Disclosure Assistance for more info.
Adam Bacchus
HackerOne is the #1 hacker-powered security platform, helping organizations find and fix critical vulnerabilities before they can be criminally exploited. As the contemporary alternative to traditional penetration testing, our bug bounty program solutions encompass vulnerability assessment, crowdsourced testing and responsible disclosure management. Discover more about our security testing solutions or Contact Us today.


