We benchmarked Claude Opus 4.7 on code-backed vulnerability validation. See accuracy gains, fewer false positives, and what it means for triage.
HackerOne Blog
The latest from HackerOne
Image
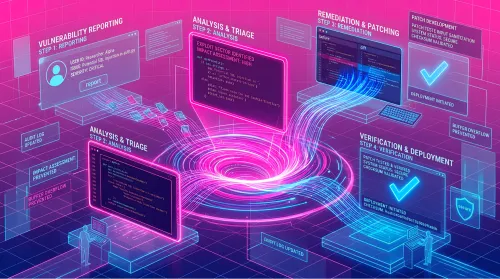
AI is making vulnerability discovery cheap. CTEM only reduces risk when teams validate exploitability, remediate, and retest to prove fixes hold.