Fact or Fiction: Mr. Robot - eps2.6succ3ss0r.p12
Hello friends, and welcome to HackerOne’s first edition of “Fact or Fiction,” where we review shows and talk about how realistic (or not!) they are. This week, we’ll be discussing...

Mr. Robot demonstrates how far we’ve come in terms of successfully weaving authentic hacking material into film. While classics like Hackers (1995) brought us loads of fun, dramatic effects and lacked realism, and Blackhat (2015) hit us with realism at the cost of the story, Mr. Robot has managed to hit all the right notes by tying together realistic hacking into a deeply layered plotline which is still accessible to general audiences.
Warning! Spoilers ahead!
If you aren’t caught up on season two, now’s your chance to turn around and pretend this blog never happened (at least, until you’re caught up, of course). For this blog entry, we’re going to focus on season two’s eighth episode, A.K.A. eps2.6succ3ss0r.p12.
Stagefright
"Stagefright" was a big Android vulnerability from last year whereby simply visiting a website on an unpatched Android phone, your phone could be hacked. Stagefright was an issue with how Android phones processed media files... so when Trenton asks what type of phone Mobley has and finds out he's on Android, she tricks him into visiting her fake benchmarking website, which in reality gives Mobley's phone a malicious "mp4" (movie file) that lets her get remote access to his phone from her computer. Pretty sneaky!
Easter eggs, and hacking Mobley’s phone
When Trenton is socially engineering Mobley into visiting her "benchmarking" website, you can see an IP address on her terminal of 192.251.68.248. If you punch that in your browser, you land at http://hioctane.dat.sh/ which looks like the "benchmarking" site that she convinces Mobley to visit. In reality, that site has a hidden stagefright exploit which allows her to own Mobley's phone.


If you go to 192.251.68.243 (the other IP address on her terminal) it brings you to http://i243.bxjyb2jvda.net/. This website is simulating Kali Linux (the operating system Trenton is using) and basically puts you in Trenton's shoes, at the point where you have hacked Mobley and can look around on his phone:

They are simulating a real terminal here... so you can actually type the following commands and find another easter egg:
- Type ls, hit enter
- Type cd sdcard, hit enter
- Type ls, hit enter
- Type cd Android, hit enter
- Type ls, hit enter
Note: You can skip the “ls” commands if you want, but it’s fun to see what the directory contents are.
At this point you've found "eat.txt". To see the contents, type cat eat.txt and hit enter.

You'll now see Mobley's notes/thoughts on a bunch of places he's eaten at. Not sure if there are any hidden clues in here or not, but it’s a pretty cool easter egg! Also, later in the episode, Mobley uses a pizza delivery guy to scope out his apartment for anything suspicious (e.g. lurking FBI agents, maybe some dark army thugs) before he goes inside himself.
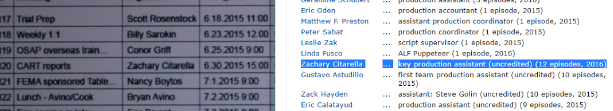
Mr. Robot staff hidden in the FBI schedule
I tried Googling some of the names in the FBI schedule of events a little after 5 minutes into the episode, and it looks like these are all names of people who work on the show! If you Look up Zachary Citarella for example, you'll find him listed as a production assistant for Mr. Robot on IMDB.
Hacking Susan Jacobs (e-corp general counsel)
When Susan knocks herself out on the wall, fsociety tries to hack her ASAP. You see Mobley pull up some software to reset her password called "ntpassword" (https://pogostick.net/~pnh/ntpasswd/ ). They are basically booting up her laptop with this software and using it to change her password and get access to her system. If her laptop was encrypted, this probably would not have worked… shame on you e-corp for not mandating full disk encryption on your laptops!

For digging through her phone, it looks like they might've used Oxygen, which is forensics software used to investigate data on mobile devices: http://www.oxygen-forensic.com/en/
Another interesting easter egg; Darlene sets Susan’s out of office reply in the episode. Have you tried emailing susan.jacobs@e-corp-usa.com?
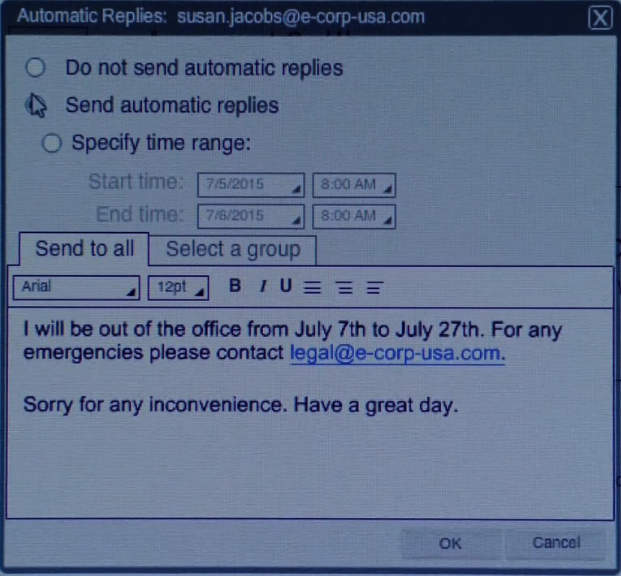
If you try emailing susan.jacobs@e-corp-usa.com, you’ll actually get the automatic reply!

Another easter egg! E-coin
When Darlene is about to pay the dude with Susan’s e-coin for use of the incinerator to dispose of her own body (harsh), she pulls out her phone and there is a QR code:

If you scan this QR code, it'll bring you to fsociety00.io, which in turn brings you to http://www.e-corp-usa.com/ecoin/, which is an advertisement for e-coin. My theory is that Price was working together with Dark Army to manipulate fsociety into being their puppets / taking the fall for the 5/9 hack, such that the economy would collapse and could be rebuilt with a currency under e-corp’s control that is worth more than existing U.S. currency. Additionally, Whiterose is in a position within the Chinese government to push for China to bail out the U.S., providing power to both Whiterose and Price. I guess we’ll see!

Wickr app
After being released by the FBI, Mobley uses an app called "Wickr" to send a message to Trenton. Wickr is a real app that offers end to end encryption, which helps ensure any messages flying back and forth between Mobley and Trenton are encrypted in transit and thus safe from prying eyes (e.g. the FBI, Dark Army, etc.) that might try to intercept it along the way. After sending the message, Mobley factory resets his phone to wipe any data or evidence off of it.
Upcoming easter egg?
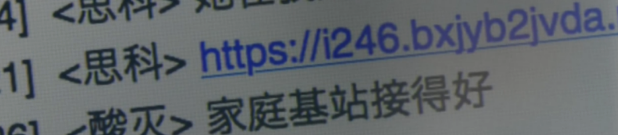
When Darlene gets on Cisco's computer and is looking at his chat messages, you can see http://i246.bxjyb2jvda.net/. I tried going there, but there's nothing at the website (yet, as of August 31, 2016). I'm guessing they may put some content up there, maybe in episode 9 or later?
Wrapping it up
There are so many easter eggs and hidden messages within Mr. Robot! Have you found any from episode 8 we missed? Let us know!
Want more Mr. Robot? Check out Adam every Thursday on ScreenJunkies Debugging Mr. Robot where he breaks down the latest episode with the crew.
Adam Bacchus
HackerOne is the #1 hacker-powered security platform, helping organizations find and fix critical vulnerabilities before they can be criminally exploited. As the contemporary alternative to traditional penetration testing, our bug bounty program solutions encompass vulnerability assessment, crowdsourced testing and responsible disclosure management. Discover more about our security testing solutions or Contact Us today.


