Software Vulnerability Disclosure in Europe: Summary and Key Highlights of the European Parliament CEPS Task Force Report

In the autumn of 2017, the Centre for European Policy Studies (CEPS), a European Union think tank, initiated a task force to define guidelines around software vulnerability disclosure (SVD) across the European Union.
In late June, the CEPS task force published their final report: Software Vulnerability Disclosure in Europe Technology, Policies and Legal Challenges. The 112-page document is worth a detailed read, but included in this post are highlights from the report and our key takeaways.
The task force’s own conclusion is that now is the time to act. The report calls upon the European Commission and member states to draft a continent-wide framework and accompanying national legislation to provide legal clarity around software vulnerability discovery and disclosure.
In an announcement titled “EU needs solid vulnerability disclosure rules” coinciding with the release of the report, Task Force Chair Marietje Schaake said “Disclosing vulnerabilities to software and hardware vendors and manufacturers is crucial to protect our digital society. If we do not seriously address this issue in EU cybersecurity policies, we are acting as if only simply rearranging the deck chairs on the Titanic.”
Read on for the TL;DR of the report, including our key takeaways. For our commentary, we will focus on The Executive Summary, and Part 1. Any sections in italics are copied directly from the report.
Executive Summary
This report puts forward the analysis, policy implications and main recommendations for the design and implementation of a forward- looking policy on software vulnerability disclosure (SVD) in Europe.
The Task Force calls upon the European Commission and the member states to collectively draft a European-level framework complemented by national legislation in accordance with the guidelines and recommendations defined in ISO/IEC 29147:2014 and ISO/IEC 30111 in order to provide legal clarity for software vulnerability discovery and disclosure.
+1,000! Clarity and consistency is important to further security research.
"It is also worth mentioning that the US Department of Justice (Cybersecurity Unit, Computer Crime and Intellectual Property Section of the Criminal Division) released in July 2017 the first version of a framework for a Vulnerability Disclosure Program for Online Systems. This framework could serve as a possible model for EU member states to consider adopting."
Yes! Our own VDP recommendations align with the DOJ Framework and NTIA template.
Based on its examination of current best practices throughout Europe, the US and Japan, the Task Force recommends implementation of various policies related to SVD. Part I of this report concentrates on CVD and Part II focuses on Government Disclosure Decision Processes (GDDP).
An abridged version of policy recommendations from the task force is included below.
Policy recommendations from the Task Force
- Amending Directive 2013/40/EU on attacks against information systems (the EU cybercrime Directive) to support CVD.
- Protection of security researchers. “The legal liability and responsibilities of security researchers should be fully clarified to enable them to continue their work without fear of prosecution.”
- Incentives for security researchers. Appropriate policies should be adopted with the aim of encouraging ‘white-hat hackers’ to actively participate in coordinated vulnerability disclosure programmes.
- Directive on security of network information systems (NIS). In transposing the NIS Directive, particularly its Article 14, member states may explicitly consider including CVD as one of the technical and organisational measures.
- General Data Protection Regulation (GDPR). According to the GDPR, software owners and tech firms become data controllers when they exercise overall control over the purpose for which, and the manner in which personal data are processed. Assuming that irresponsible handling of vulnerabilities could lead to personal data breaches falling within the scope of GDPR, CVD should be viewed as one of the necessary tools to mitigate the relevant risks.
- Cybersecurity Act Amendments. State that ENISA can contribute to the harmonised development of CVD in the EU by having its mandate amended. A provision in Article 47 (1)j of the Cybersecurity Act provides the possibility to introduce CVD in a European Cybersecurity Certification Scheme, which in fact may encourage CVD as a standard practice.
- Software vulnerabilities in durable goods such as cars and medical devices
- Amending national legislation to support CVD
- Framework Programmes for Research and Innovation (focus on EU research funding)
- GDDP characteristics recommended to adopt (GDDP is the EU version of The United States’ Vulnerabilities Equities Process) and survey of member states’ GDDP is also suggested.
Part 1: Coordinated Vulnerability Disclosure in Europe
This is the bulk of the report. The Task Force reviews and enforces their definition of terms, leaning heavily on the impressive work compiled in the CERT Guide to Coordinated Vulnerability Disclosure.
Section 3.1 addresses the current state of CVD within EU member states.
Interesting analysis captured in the graph below.
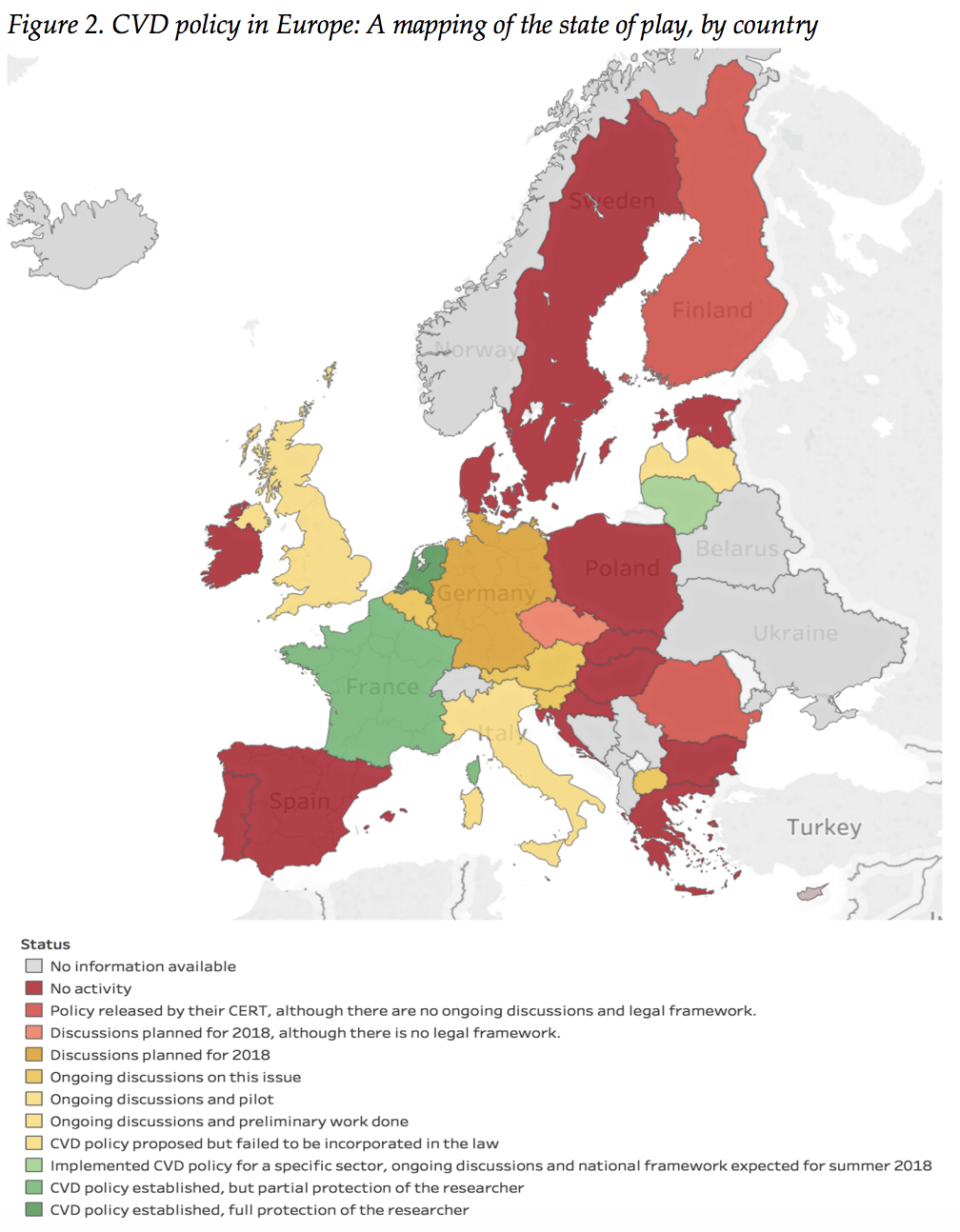
The Netherlands was the first country to embrace CVD. They’re at the positive extreme, offering full protection for researchers, while France has similar national policies, but offers only partial protections to researchers. Ten other European countries have policies in progress, but nearly 20 have little or no national activity related to CVD.
Section 3.2 and 3.3 includes case studies of two EU member states, The Netherlands and Latvia and two examples of countries external to the EU: United States and Japan.
“Some governments, such as the Netherlands, have been quite active in this area and, together with the private sector and the security research community, developed as early as 2013 a model of coordinated vulnerability disclosure.”
Director of Cybersecurity Initiatives at NTIA in the US Dept of Commerce, Allan Friedman wrote the US history of CVD section. He tweeted that the report “acknowledged need for more legal harmonization and protection, but also noted importance of private sector leadership, building on existing work, incl DoJ & NTIA.”
Section 4 Addresses the legal challenges from software vulnerability disclosure in the EU
This is a look at the benefits and risks in the current environment. HackerOne has published several resources with commentary from US-based legal experts as well. See: Attorneys Chime in on Hacker-Powered Security, and How Corporate Counsel Should Approach Hacker-Powered Security.
Section 5 and 6 Review policy implications and recommendations for implementing CVD in Europe (including GDPR).
Section 6.2.5 specifically addresses GDPR. Some landmark notes in here, including "If a controller implements a CVD programme allowing vulnerabilities to be dealt with in a timely manner, then it may reduce the risk of incurring fines arising from possible personal data breaches.”
Big note! Implementing a vulnerability disclosure policy reduces risk of a breach and corresponding GDPR fines.
“...With respect to the open question as to if and when CVD may constitute unlawful processing of personal data, it is worth referring to recital 49, which seems to suggest that researchers may potentially be able to argue that to the extent they disclose such activities to the data controller in the context of CVD, such disclosure may fall within the scope of a legitimate interest of the controller in preventing security breaches by fostering network and information security. It would therefore then be up to the data controller to demonstrate that CVD was implemented with the intention of ensuring a higher level of network and information security, thereby serving its legitimate interest.”
This is a key section for the hacker-powered security industry, noting that when a CVD is in place, it is essentially not a security incident, but activities in the legitimate interest of the controller to prevent a breach.
HackerOne’s Key Takeaways
In the background section of the report, the authors note that the debate on how to handle the disclosure of insecurities pre-dates software security. Today, in the 21st century, we can still take lessons from 1850s locksmiths. In The Rudimentary Treatise on the Construction of Locks, locksmith Alfred Hobbes noted “it is to the interest of honest persons to know about [insecurities], because the dishonest are tolerably certain to be the first to apply the knowledge practically."
This is a relevant truth for us today.
Protect the Researchers
Many organizations agree that vulnerability disclosure is a valuable tool, and, the CEPS report states, white-hat hackers discovering vulnerabilities are in need of protection. This safe harbor is critical to enabling the beneficial disclosure that CEPS and so many others are touting.
"Protection of security researchers. Researchers involved in vulnerability discovery are often exposed to criminal or civil liability. The legal liability and responsibilities of security researchers should be fully clarified to enable them to continue their work without fear of prosecution." - Safe Harbor is critical to enabling security research.” - Section 6.2.2, Protection of Security Researchers
CVD doesn’t work if researchers fear for their safety when making honest disclosures. Researchers should have clear and adequate protections at the highest level.
CVD is essentially a Requirement under GDPR
GDPR is still in its infancy, but it’s impact is already being felt by organizations across the globe. The CEPS report doubles down on GDPR’s relevance to CVD, going so far as to say “irresponsible handling of vulnerabilities could lead to personal data breaches falling within the scope of GDPR, CVD should be viewed as one of the necessary tools to mitigate the relevant risks."
In short, irresponsible handling of vulnerabilities is a violation of GDPR. So have a CVD to avoid liability under GDPR.
Furthermore, CEPS says that the mere presence of a CVD and the timely handling of vulnerabilities “may reduce the risk of incurring fines arising from possible personal data breaches." Read another way, the absence of a CVD could be seen as not only irresponsible, but worthy of penalties.
CEPS further clarifies that, under GDPR’s concerns over processing of personal data, CVDs should be considered “of a legitimate interest of the controller in preventing security breaches by fostering network and information security.” Therefore activities conducted under the scope of a CVD do not constitute a breach of data under GDPR, further indicating protection for researchers.
Governments Should Disclose Vulnerabilities by Default
The U.S. government’s VEP leans towards disclosing vulnerabilities in nearly all cases. CEPS echoes that by recommending the “default policy should be to disclose vulnerabilities immediately to the affected vendor(s) so they can be patched."
Conclusion: The Time to Act is Now
HackerOne agrees with CEPS that disclosure is in the national interest and security researchers are providing a public benefit that should be protected. In the U.S., many government agencies and organizations are either pioneering hacker-powered security efforts with VDPs and bug bounties, or they are recommending that constituent organizations implement VDPs. In the EU, it’s important to take the same steps to maintain pace with technology, modern efforts to secure it, and the criminals exploiting vulnerabilities.
We support the following specific initiatives:
- Legislation and/or policies at the national level to offer safe harbor protections to researchers who discover and responsibly report vulnerabilities.
- Providing incentives to those security researchers, since their efforts are valuable to both the organizations and the public at large.
- Imploring organizations of all sizes and sectors to implement CVDs as an effective tool to mitigate risks, including leveraging CVDs as an effective component of GDPR compliance.
In many ways, the public sector is leading the private sector in the realm of vulnerability disclosure policy adoption and proliferation. We support the broad adoption of CVD as it benefits the safety of our connected society, aligning with our mission to empower the world to build a safer internet.
If you’re looking to learn more about how to effectively work with ethical hackers, start a conversation today to see what steps you can take now and how HackerOne can help.


