Hack the Pentagon
Hack The Pentagon is a bug bounty program of the US Department of Defense on the HackerOne Platform

Innovative Pilot Launch
The US Department of Defense’s Defense Digital Service (DDS) team pioneered the Hack the Pentagon bug bounty pilot program with strong support from Secretary of Defense Ash Carter. The pilot ran from April 18, 2016 until May 12, 2016 and exceeded all expectations.
Hack the Pentagon was the first bug bounty program in the history of the Federal Government. The Department of Defense selected HackerOne as its partner to advise, operate, and execute Hack the Pentagon.
On March 31, 2016, interested participants began registration to compete in the "Hack the Pentagon” pilot challenge.
The pilot program was designed to identify and resolve security vulnerabilities within Defense Department public facing websites through crowdsourced security.
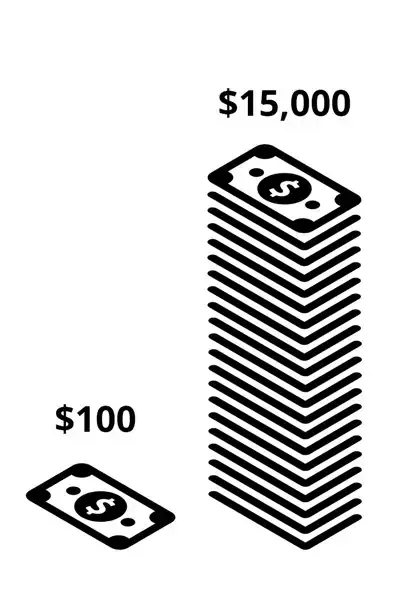
Individual payouts ranged from $100 to $15,000
Results That Exceeded Expectations
13 Minutes
Time to first vulnerability after program officially launched.
Time to first vulnerability after program officially launched.
200 Reports in 6 Hours
Were submitted immediately after launch.
Were submitted immediately after launch.
1410 Hackers
Registered to participated in the program.
Registered to participated in the program.
$75,000 Bounties Paid
For all legitimate vulnerability reports.
For all legitimate vulnerability reports.
Hack the Pentagon challenge
On April 18, 2016, Hack the Pentagon challenge opened for submissions. The first report arrived in 13 minutes from that launch. Just six hours later, that number grew to nearly 200. During the pilot program, a new report came in every 30 minutes on average. HackerOne provided triage services to assist the Department of Defense, allowing them only focus on the valid reports
More than 1,400 participants registered to take part in Hack the Pentagon. Of those, 250 eligible hackers submitted a vulnerability report. Out of all the submissions, 138 were found to be "legitimate, unique and eligible for a bounty," and resolved according to Defense Secretary Ash Carter. Those vulnerabilities earned $75,000 in total bounty rewards, paid promptly by HackerOne at the conclusion of the program.
More on Hack the Pentagon
Hack the Pentagon Again, and Again
The Department of Defense announces plans to expand upon Hack the Pentagon
The Department of Defense announces plans to expand upon Hack the Pentagon
What Was it Like to Hack the Pentagon?
A behind the scenes look at Hack the Pentagon from Marten Mickos, CEO, HackerOne
A behind the scenes look at Hack the Pentagon from Marten Mickos, CEO, HackerOne
Fact Sheet About Hack the Pentagon
An overview of results from the first cyber bug bounty program in the history of the Federal Government.
Learn More
An overview of results from the first cyber bug bounty program in the history of the Federal Government.
Learn More