UK Insurance Company eliminates systemic injection risk
By extending a scheduled web application pentest paired with Agentic Pentest as a Service, the organization broadened injection coverage, validated remediation before release, and strengthened risk assurance without expanding budget.

Overview
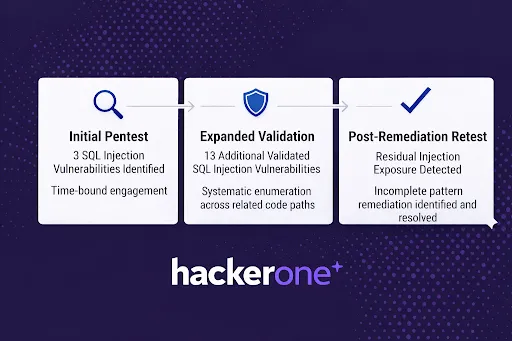
Ahead of a production release, a UK-based insurance provider conducted a scheduled web application pentest on its underwriting platform. The test identified 3 SQL injection vulnerabilities.
Rather than focusing on the count, security leadership focused on the implications that the vulnerability could be systemic and not comprehensively addressed prior to release.
To answer that question, the organization extended the engagement using HackerOne’s Agentic Pentest as a Service (PTaaS). Following confirmation that SQL injection existed, Agentic PTaaS systematically evaluated related query paths to determine whether similar exposure existed elsewhere. The result was a 4x increase in confirmed SQL injection coverage and the discovery of residual exposure after remediation had been considered complete.
The organization moved from isolated findings to a complete account of the risk, without increasing pentest scope or cost.
SQL Injection as a System Pattern, Not an Isolated Defect
The underwriting platform supports complex workflows and processes sensitive data across multiple industries. Release approvals require more than proof that issues were found; they require confidence that systemic risk has been reasonably contained.
The initial pentest provided depth and adversarial context. What it could not definitively answer within a fixed engagement window was whether the vulnerability class extended beyond what had been observed.
For the team, the main concerns were:
If injection surfaced in several places, was it a pattern?
And if it was a pattern, how could remediation be validated before release?
Continuous Agentic Validation Reveals Systemic Exposure
Agentic PTaaS was introduced to determine whether the confirmed vulnerability class extended beyond the initially identified endpoints. The confirmed presence of SQL injection informed focused validation of similar input-handling patterns across the application. Agentic reconnaissance was initiated to identify all related and similarly designed query paths throughout the application, exploit them to test for the absence of prevention controls, and validate their reproducibility and business impact.
In doing this, it identified 13 additional validated SQL injection vulnerabilities across related query paths that were outside the time-bound focus of the original engagement.
Across both approaches, a total of 16 validated SQL injection vulnerabilities were confirmed. This represented more than a 4x expansion in SQL injection coverage without increasing pentest hours or engagement scope.
The expanded coverage extended the initial pentest, building on the initial confirmation of SQL injection by systematically evaluating similar application pathways. Every additional pentest finding included:
- Reproducible proof of exploitability
- Clear execution evidence
- Qualified human expert confirmation prior to reporting
The expansion showed that SQL injection was not limited to 3 endpoints but was a widespread input-handling flaw across the application, requiring dedicated remediation in every instance.
Closing the Gap Between Fix and Assurance
Following remediation, the security team requested validation of the fixes. Initial remediation addressed a subset of the reported vulnerabilities. However, follow-up agentic testing consistently identified unresolved SQL injection exposures. In several cases, individual injection paths had been patched, but related code paths remained vulnerable. This provided the organization with remediation verification in real-time as findings were progressively resolved.
Without retesting, these issues would likely have been considered resolved. Instead, the organization identified precisely where remediation was incomplete and applied additional fixes prior to release. Importantly, systematic validation enabled rapid confirmation between scheduled pentest cycles, rather than waiting for a future engagement window.
Validation Cycles Shrink From Weeks to Hours, Reducing Friction and Incident Risk
Agentic PTaaS transformed a point-in-time assessment into a validated, meaningful risk reduction. It identified injection patterns, understood the exploitation context, systematically validated whether the pattern existed elsewhere, and enabled rapid revalidation after fixes.
Release approval was supported by evidence-backed assurance rather than assumption.
Coverage expanded significantly without expanding scope or budget.
The team avoided overconfidence and strengthened its internal risk narrative.
The team avoided overconfidence and strengthened its internal risk narrative.
Validation cycles shortened.
Remediation could be confirmed within the same operational window, reducing friction and improving release confidence.
Remediation could be confirmed within the same operational window, reducing friction and improving release confidence.
Catching Repeat Issues Early So Small Bugs Don’t Become Big Incidents
This experience marked a shift from point-in-time testing to a continuous threat exposure management operating model, where each exposure progresses through discovery, confirmation of exploitability, risk-based prioritization, and remediation before production.
That same model will be applied to high-risk workflows, dynamic input handling areas, and complex integrations. As development velocity increases, validation must scale accordingly. Ongoing discovery, exploit verification, and regression testing act as control gates across the software lifecycle to limit the introduction of new risk.
Release confidence is grounded in proven exploitability and completed remediation. Confidence before release is now a standard operating expectation.