Vetted Cybersecurity Partners
HackerOne Clear and HackerOne Gateway bring decreased risk and fine-tuned control to your security programs. Partner with proven, ID-verified, and background-checked security researchers with the skills and reputation to match your specific needs.
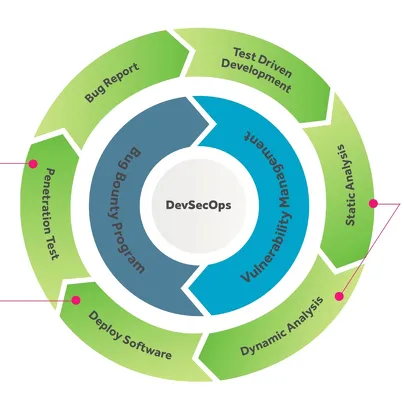
How it works
HackerOne Clear can be added to any HackerOne private program, bolstering your existing security efforts. Clear connects you with talented, ID-verified, background-checked, citizenship checked and/or residency-checked security researchers from our million-strong community, providing 24x7x365 coverage for your most sensitive assets.
Gateway utilizes Cloudflare’s Zero Trust Network (ZTNA) functionality to bring crowdsourced security to your attack surfaces through IP whitelisting. It allows for program traffic to be routed through HackerOne’s Gateway ZTNA, capturing researcher traffic data, providing transparency on all testing activities and allowing customers to have real time control on who can access their program, when.
Researchers vetted by Clear hail from over 60 countries and have identified more than 65,099 valid vulnerabilities, including over 44,524 critical and high-severity vulnerabilities in the last two years. Specialized Clear researchers also have varying levels of US federal government clearances.
Gateway provides full visibility into your testing activities, giving you confidence in your coverage and transparency for your stakeholders.

Clear gives even the most risk-averse organizations the confidence to bring third-party security researchers into their security programs. Clear screens researchers using a combination of ID verification, background checks, citizenship & residency checks, digital click-through agreements, reputation scores, and Code of Conduct reviews, plus includes real-world skills validation to ensure researchers have the expertise to uncover high-impact vulnerabilities.

Gateway routes all security program traffic through HackerOne’s Gateway ZTNA, providing the additional traceability required in highly regulated industries. It even enables external security researchers to test pre-production assets, with IP whitelisting and granular controls down to the individual researcher. Plus, Gateway features split tunnel, researcher-level segregation, and logging with TLS decryption.
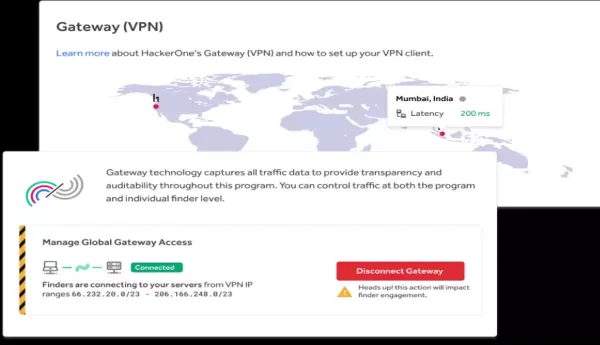
Transparency and Control
Confident Assurance
- Know your researchers. Partner with ID-verified, background-checked, citizenship-checked and/or residency-checked security researchers so you know they have the right skills and experience.
- Ensure compliance. Comply with regulations, standards, and audit-based requirements.
Enhanced Visibility
- Secure access. Provide access to assets behind the firewall by whitelisting HackerOne’s Gateway IPs.
- Secure any scope. Enable secure testing across the most sensitive attack surfaces.
Access the World’s Elite Security Researchers
Only the most elite security researchers are chosen to participate in HackerOne Clear programs, adhering to HackerOne’s Code of Conduct. If a HackerOne program explicitly requires testing via the Gateway, security researchers will adhere to that restriction, as well.
Rigorous Vetting for Quality and Security
The best security researchers want to work with organizations who demand more. But those researchers also expect more: transparency, a speedy resolution of reported issues, and public recognition. They look for a rich bounty table structure, an engaging and competitive scope, and a direct relationship with your program management team to continuously improve the program.