The Vulnerability Apocalypse Is a Remediation Crisis

As the largest vulnerability coordination platform across enterprise and open source, HackerOne has a unique vantage point on our evolving AI world. Here's what the data says.
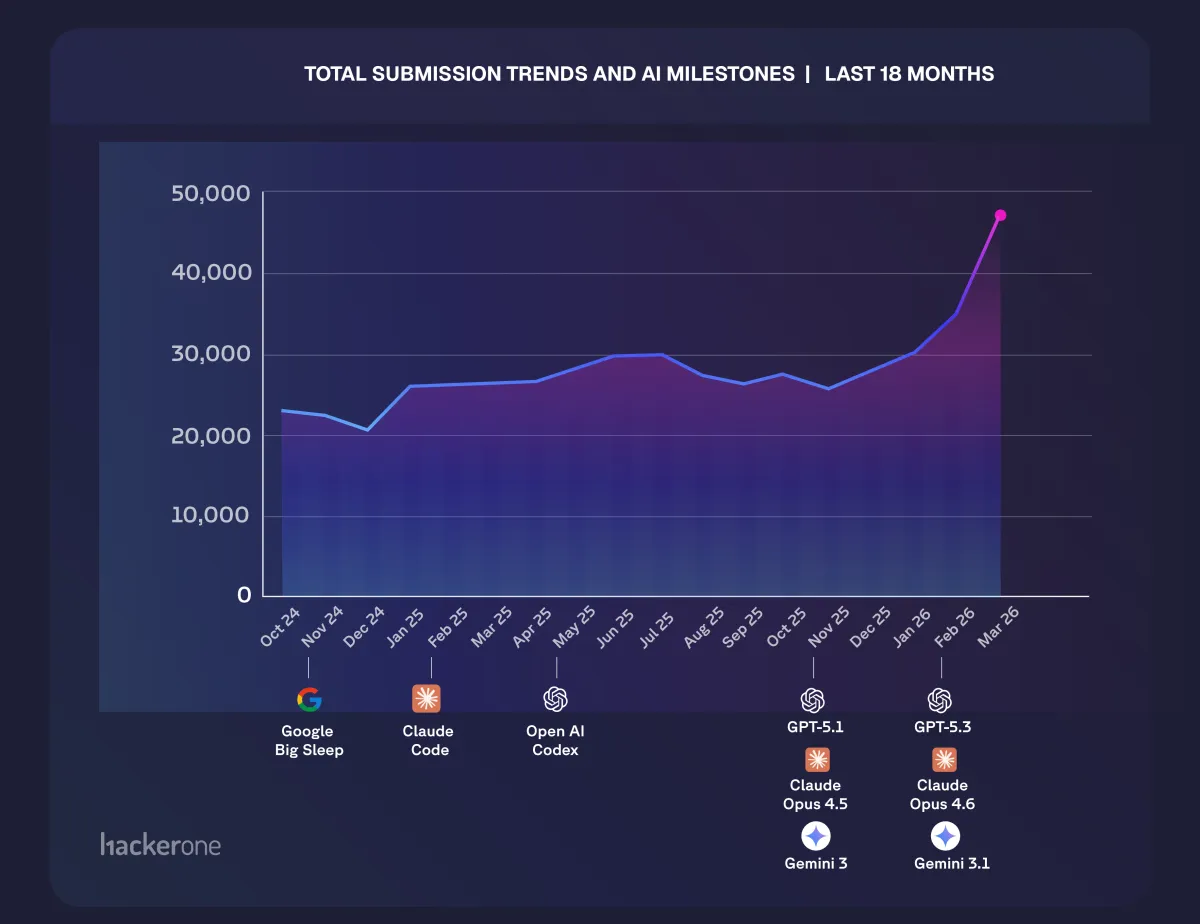
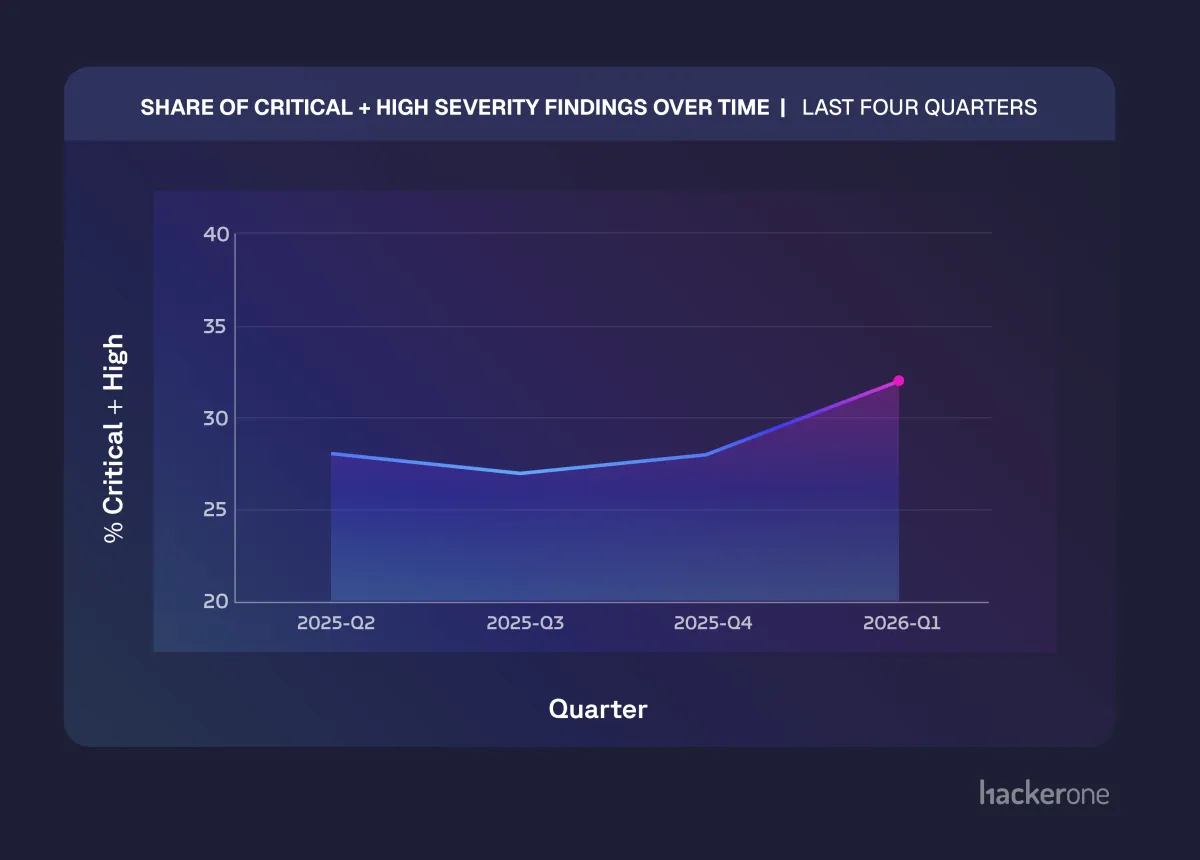
Vulnerability submissions on the HackerOne platform reached an all-time high in March 2026: 46,947 total submissions, a 76% increase year over year. The percentage of valid, exploitable vulnerabilities held steady at roughly 25%. That means the absolute number of confirmed, exploitable findings arriving on defenders' desks has grown proportionally. The share of critical and high-severity vulnerabilities has climbed to 32% of validated findings, up from a historical baseline of 26-28%. Meanwhile, remediation throughput has shown only slight improvement with defenders fixing about 19% more vulnerabilities than a year ago, meaning backlogs have also reached an all-time high this month.
The world is changing. Vulnerability discovery is up 76%. Severity is climbing. Signal is holding stable. But the overall fix rate isn't keeping pace and the backlog is growing. The rest of this post is about what's driving it, why it matters, and what to do about it.
The Signal is Real
When volume spikes, the natural question is: how much of this is noise?
We asked ourselves the same question. The answer is that the signal-to-noise ratio hasn't changed. The roughly 25% validation rate on our platform has held steady through the entire growth curve. What's changed is the denominator. At 46,947 submissions, that's a lot of real, exploitable vulnerabilities coming in at an accelerating pace.
As AI-assisted submissions have grown, we've invested heavily in AI-powered triage and validation on our own platform. Our agentic AI system, Hai, now handles initial classification, deduplication, and validation of incoming reports, working alongside our human security analysts. The principle is straightforward: if AI is accelerating discovery, AI also needs to accelerate the validation layer, or the entire pipeline backs up. Regardless of where a vulnerability report comes from, the triage process needs to verify the finding, confirm it's in scope, assess severity, route it to the right team, propose a remediation, and validate that remediation. Without this continuing investment, we would not be processing the volume we're seeing today.
This same challenge applies to every organization receiving vulnerability reports. The validation and triage layer is what converts raw volume into actionable signal. If you don't have one that scales, the volume becomes a liability rather than an advantage.
This is Not the AI Singularity
The narrative matters, so let me be precise about what is driving this.
This is not a story about a single frontier model autonomously finding every bug. It's a story about hundreds of thousands of human researchers, with different backgrounds, different toolchains, and different intuitions about where to look, using AI to amplify and scale capabilities they already had. Researchers now build their own harnesses around these AI models to scale their tradecraft. A researcher who spent years on authentication logic now tests that logic across ten times more targets. A team that specializes in mobile APIs uses AI to automate the reachability analysis that used to consume half their engagement time. A top security consultancy goes AI Native then observes productivity increase by an order of magnitude.
The severity of the signal has shifted. Researchers aren't just finding more of the same. The 32% critical-and-high share, up from a historically stable 26-28% baseline, tells us that AI-assisted researchers are going deeper: identifying exploit chains that combine multiple lower-severity issues into high-impact attack paths, reaching code paths that automated scanners and manual review have missed for years.
The diversity of human perspective is the force multiplier. AI raises the floor of what any individual researcher can accomplish. The breadth and creativity of the security research community determines where that capability gets pointed.
The curl project tells this story clearly. A year ago, curl's maintainer Daniel Stenberg was vocal about low-quality AI-generated reports overwhelming his small team. That was a real problem. Fast-forward to April 2026, and Stenberg posted a very different update: the slop is gone, replaced by an increasing stream of high-quality security reports, almost all done with AI assistance, arriving faster than ever.
That shift from noise to signal is what happens when skilled researchers adopt better tools. More valid findings, from more diverse sources, requiring more structured coordination. The discovery side is working. The fix side is where the system is under stress.
The challenge now is building the validation and remediation infrastructure to keep up with the output.
The Remediation Crisis
Here is the number that should concern every technology leader reading this.
Our data shows a clear and growing gap between the rate at which valid vulnerabilities are discovered and the rate at which organizations remediate them. The good news is real: our customers are fixing critical issues faster. Median time to remediate critical findings has dropped to under 15 days over the past year. Security teams have internalized that critical vulnerabilities demand immediate action, and they are executing, increasingly with the assistance of AI.
The harder truth: overall remediation throughput has only increased by 19%, against a volume increase of 76%. The backlog is growing. Every day a validated finding sits unresolved, it represents an exploitable window. Attackers now have the same AI tools to discover and weaponize those findings in hours, not months.
For years, the industry's risk calculus was built on scarcity. Most vulnerabilities would never be found because the work was too hard, too specialized, and too expensive. That assumption no longer holds. When a skilled researcher can point an AI agent at a codebase and wake up to a working exploit, the economics of offense have fundamentally changed. The Zero Day Clock further illustrates how the time between disclosure and weaponization has collapsed to hours.
The bottleneck is not discovery. It is the find-to-fix cycle.
The organizations pulling ahead right now are not the ones finding the most vulnerabilities. They are the ones that can triage, validate, prioritize, and fix the most critical issues fastest. Phil Venables described it simply: speed is the only fundamental defense.
What the Data Says to Do
I've had dozens of conversations with security teams over the past month. The ones keeping pace share a few things in common, and they map directly to what we see in the platform data.
Re-tool validation and remediation for speed, not just coverage. Traditional vulnerability management was built for periodic batches: quarterly pentests, annual assessments, monthly scan reports. That cadence is obsolete. The organizations adapting fastest have collapsed their triage-to-fix pipeline with AI-assisted prioritization, automated validation, direct integration between vulnerability intake and engineering workflows, and AI code fixes. Manual approval steps add delay, and delay is now the primary risk.
Treat vulnerability intake as a continuous operation. If your security program still treats external vulnerability reports as exceptions to normal workflow, it is not ready for what's coming. Anthropic's recommendation to prepare for an order-of-magnitude increase in finding volume is not hypothetical. We are seeing it. Build always-on intake, triage, and response capabilities that can absorb sustained volume from diverse sources: live attacks, bug bounty researchers, automated scanners, AI agents, and internal tooling alike. The validation layer, whether you build it or use a platform like ours, is what makes volume manageable rather than overwhelming.
Leverage AI to fix classes of bugs, not individual findings. When AI surfaces the same category of vulnerability across dozens of endpoints, the right response is not fifty individual patches. It's a systemic fix at the framework or architecture level. Find the 20% of work that eliminates 80% of current and future vulnerability surface. That is the highest-leverage investment a security team can make right now.
Embrace external perspective as a structural advantage. Defenders control the environment, the data, and the context. That's a real advantage, but it only materializes if you are actively seeking signal from outside your walls. The researchers on our platform bring thousands of distinct perspectives and areas of expertise. No internal team replicates that breadth. AI amplifies each of those perspectives. The result is the most comprehensive view of your attack surface that has ever been possible.
What Comes Next
We are at the front end of a structural shift in how vulnerabilities are discovered, reported, validated, and remediated. The volume will continue to increase. The severity will continue to climb. The window between discovery and exploitation will continue to shrink. The Cloud Security Alliance (CSA) "Mythos-ready" strategy briefing frames this as "the first of many waves," and we think that's right.
The security community has faced capability step-changes before: automated scanning, the professionalization of offensive security, the explosion of cloud attack surface. Each time, the organizations that adapted fastest came out stronger. This time the pace is faster and the stakes are higher.
The hype is not unfounded. Our data confirms it. The advantage now goes to defenders that can validate and fix critical issues fastest. The discovery problem is being solved first. The remediation problem is the one that will define who is secure and who is exposed over the next two years.
The best time to re-tool for speed was a year ago. The second best time is now.



