Hack The Pentagon Turns One on HackerOne

Great news for U.S. citizens! Over 3,000 valid security vulnerabilities have been resolved with the U.S. Department of Defense’s “Hack the Pentagon” hacker-powered security program.
Just over a year ago, following the success of the pilot, we announced the U.S. Department of Defense was expanding its “Hack the Pentagon,” initiatives. To date, HackerOne and DoD have run bug bounty challenges for Hack the Pentagon, Hack the Army and Hack the Air Force.
The success of these programs has been undeniable and our amazing community of hackers continues to impress even us!
DoD has resolved nearly 500 vulnerabilities in public facing systems with bug bounty challenges and hackers have earned over $300,000 in bounties for their contributions -- exceeding expectations and saving the DoD millions of dollars. You can read more in our recent case study “Defending the Federal Government from Cyber Attacks.”
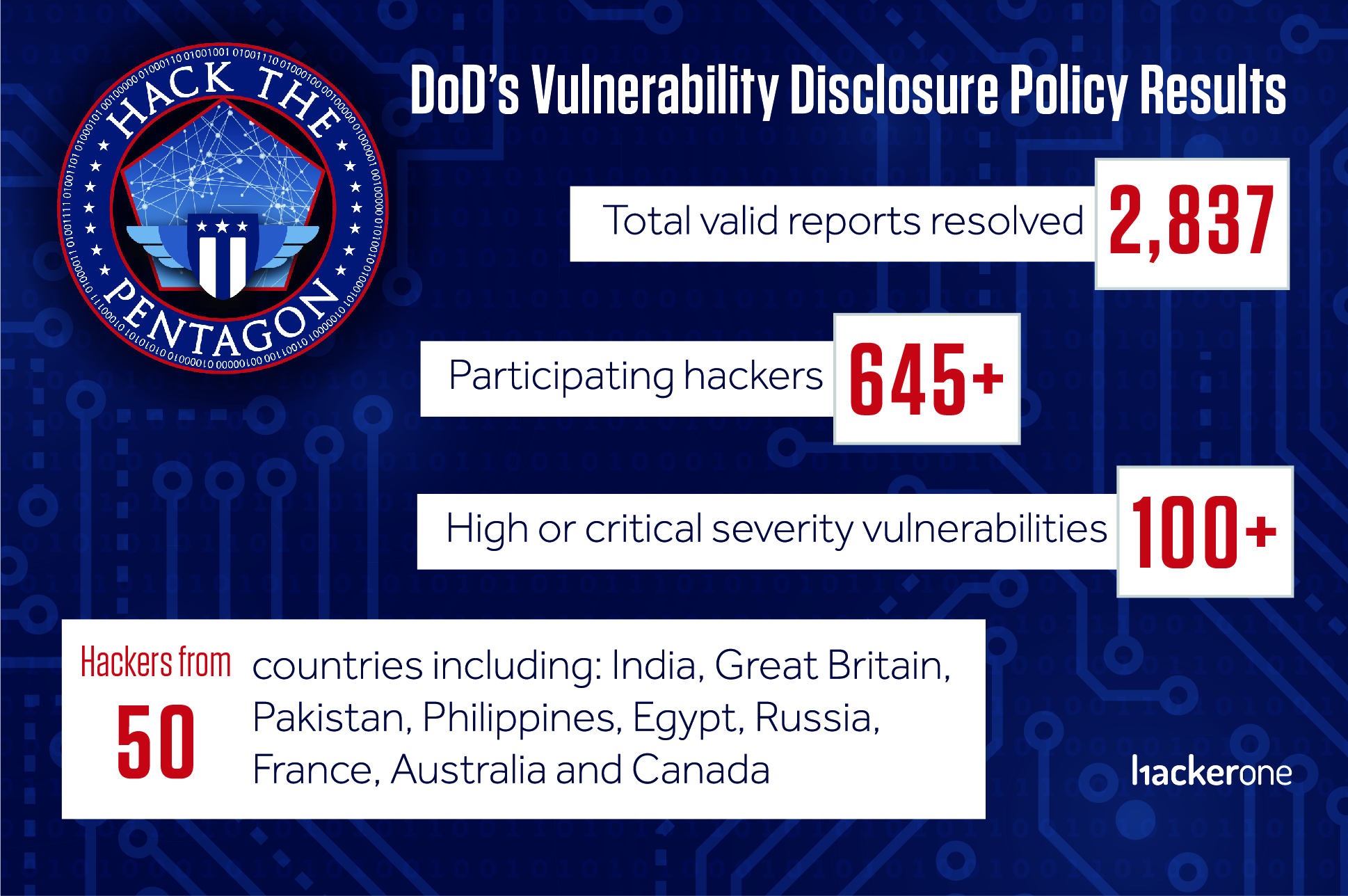
2,837 Bugs Resolved With DoD’s Vulnerability Disclosure Policy
The DoD’s Vulnerability Disclosure Policy (VDP) is another essential, likely less talked about, part of the Hack the Pentagon initiative pioneered by DoD’s Defense Digital Service team.
A VDP is the, “see something say something of the internet”. DoD’s policy, and others like it, provide clear guidance for any hacker anywhere in the world to safely report a potential vulnerability so it can be resolved. Maintaining the security of the DoD’s networks is a top priority and their VDP is another proven way to resolve unknown security issues.
While a bounty or cash incentives are not awarded for vulnerabilities reported through the VDP, that has not stopped hackers eager to do their part to help protect the DoD’s assets. Nearly 650 hackers from more than 50 countries have successfully reported valid vulnerabilities through the VDP.
Thanks to these hackers and the pioneering team at DoD, 2,837 security vulnerabilities have been resolved in nearly 40 DoD components. Of these vulnerabilities, over 100 have been high or critical severity issues, including remote code executions, SQL injections, and ways to bypass authentication.
While the majority of participating hackers have been from United States, the top contributing countries include India, Great Britain, Pakistan, Philippines, Egypt, Russia, France, Australia and Canada.
Paving the Way to a more secure nation with Hack the Pentagon
Hack the Pentagon’s successful hacker-powered programs continue to pave the way for other federal agencies and organization committed to improving security.
These leading organization include, the General Service Administration’s 18F who announced their bug bounty program in May, 2017.
The U.S. Department of Justice released an official Vulnerability Disclosure Program framework to help any agency or organization run a successful vulnerability disclosure policy. The IoT Cybersecurity Improvement Act of 2017, will require vendors to have a VDP for any internet-connected device used by the federal government.
The Internal Revenue Service are leveraging hacker-powered security and congress approved legislation for Department of Homeland Security to run the “Hack DHS” bug bounty program just last month.
No organization or government is so powerful that it does not need outside help identifying security issues. The DoD is leading by example and setting a new standard for inclusion and community in cybersecurity. Working with the external hacker community continues to supplement the amazing cybersecurity work that the DoD team is doing internally.
Eager to hack on these programs? Check back in a few weeks for our next bug bounty challenge or check out the DoD’s VDP program and guidelines to get started hacking today: https://hackerone.com/deptofdefense
HackerOne is the #1 hacker-powered security platform, helping organizations find and fix critical vulnerabilities before they can be criminally exploited. As the contemporary alternative to traditional penetration testing, our bug bounty program solutions encompass vulnerability assessment, crowdsourced testing and responsible disclosure management. Discover more about our security testing solutions or Contact Us today.


