From Valid Findings to Proven Risk Reduction
Built for teams running a mature bug bounty across high-value web and API assets—so real-world exploit findings and verified fixes scale continuously across your entire attack surface.

Bug Bounty Works. Validation Is the Bottleneck.
Your bug bounty program delivers high-quality findings and real attacker insight.
But most teams hit the same wall:
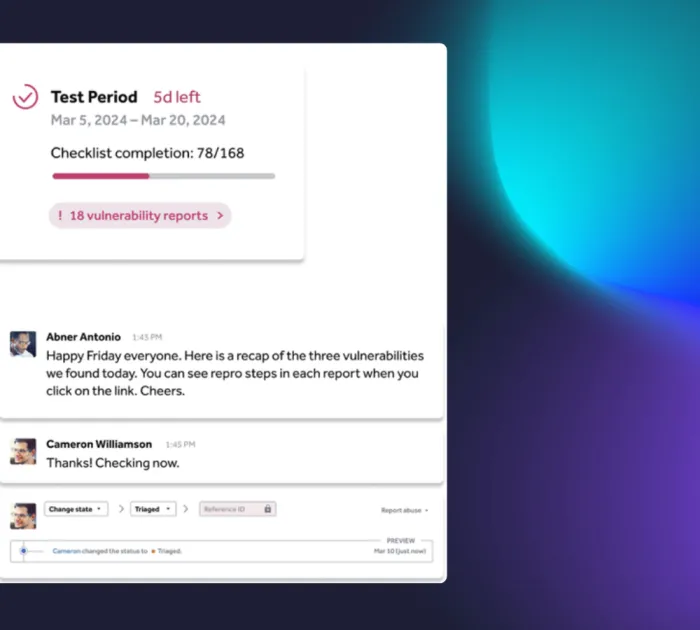
- Valid vulnerabilities still need deep validation
- Severity doesn’t always equal exploitability
- Fixes aren’t continuously re-tested as code changes
- Elite human expertise doesn’t scale across every finding
That gap is where risk lingers.
This Does Not Replace Bug Bounty
It Extends the Value of Proven Exploitation with Real Fixes
Bug bounty excels at uncovering real, attacker-driven exploitation.
Agentic PTaaS builds on that foundation by extending continuous adversarial validation across more of the attack surface between bounty activity.
It focuses on what happens next:
- Can this be exploited in your environment?
- Can multiple findings be chained into real attack paths?
- Did the fix actually eliminate risk—or just close the ticket?
Agentic PTaaS applies continuous, adversarial pressure after discovery—helping ensure that the same standard of proof delivered by bug bounty holds over time and across change
Bug bounty provides high-confidence discovery and proven exploitation.
Agentic PTaaS extends that same level of accuracy and judgment across a broader attack surface with continuous, scalable validation.
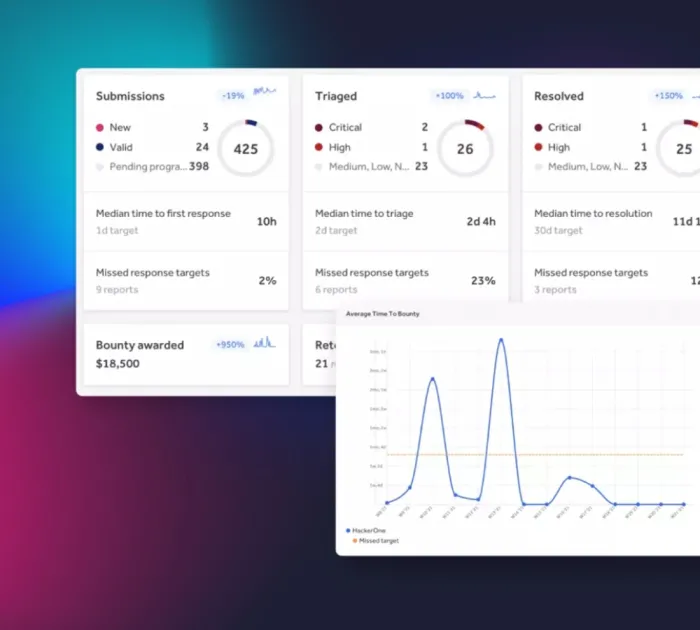
Together, they operationalize a true Continue Threat Exposure Management (CTEM) workflow at scale:
Discovery
combining your existing bounty program with agentic pentesting
combining your existing bounty program with agentic pentesting
Validation
for single view of what needs fixed
for single view of what needs fixed
Prioritization
based on proven exploitability
based on proven exploitability
Remediation & Retesting
with defensible closure
with defensible closure