Headline: Validated Exploitability for [CUSTOMER’S PRODUCT]
Built for teams running a mature bug bounty across high-value web and API assets—so real-world exploit findings and verified fixes scale continuously across your entire attack surface.

Scale the Program. Speed Up the Defense.
You’ve built one of the world’s most mature bug bounty programs, engaging thousands of researchers to protect a platform serving [Number of end users]. Agentic PTaaS builds on that foundation by validating exploitability in current environments.
Since launching its bug bounty program in [year], [account name] has evolved from internal reporting to full participation in the HackerOne network — driving real, exploitable findings and production fixes that continuously strengthen [account name’s] defenses.
Continuous discovery is your advantage. Agentic PTaaS extends it with continuous exploit validation.
What’s Possible With Agentic PTaaS at [[account name]]’s Scale
You’ve built a bug bounty program that reliably surfaces real exploit findings and drives fixes.
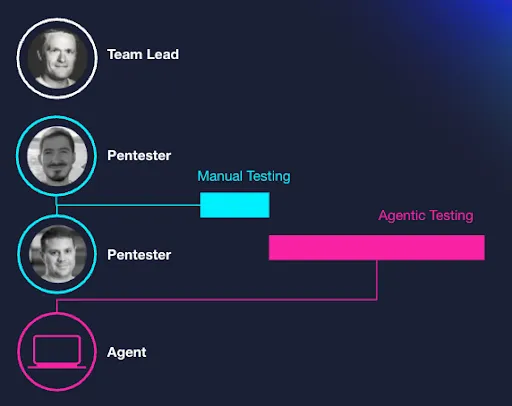
Agentic PTaaS is the next, complementary layer: continuous, expert-verified pentesting that applies that same rigor everywhere your attack surface is expanding. AI brings the scale and machine-speed across your attack surface, while human insights ensures high accuracy and judgement to expose your risk and eliminate it - continuously.
Exploit findings
need to be validated consistently as environments change including new AI systems
need to be validated consistently as environments change including new AI systems
Severity alone
does not always reflect real-world risk
does not always reflect real-world risk
Fixes need
to be re-tested as code and configurations evolve
to be re-tested as code and configurations evolve
Human-led
Expertise is powerful, but difficult to apply continuously everywhere
Expertise is powerful, but difficult to apply continuously everywhere
Why Bug Bounty Leaders add Agentic PTaaS
Bug bounty provides high-confidence discovery and proven exploitation.
Agentic PTaaS extends that same level of accuracy and judgment across a broader attack surface with continuous, scalable validation.
- Discovery combining your existing bounty program with agentic pentesting
- Validation for single view of what needs fixed
- Prioritization based on proven exploitability
- Remediation & Retesting with defensible closure
[David Schechter]
Senior Account Executive
East Coast