The IoT Security Foundation’s fifth annual report into the state of vulnerability disclosure consumer Internet of Things, produced by Copper Horse and supported by HackerOne, found that despite legislation and regulation being brought in by governments around the world, companies are still failing to implement mechanisms for security researchers to be able to report vulnerabilities in products and services. This includes big names that sell expensive products that you think would know better. These companies have lawyers and public policy people so they should realise that legislation is heading their way.
The emergence of vulnerability disclosure and bug bounty programs as a best practices over the past few years has been a welcome positive in an industry where we often concentrate on the negative aspects of security. The best thing about it is that the hacking community, who have shown the way in terms of intellectual leadership, were largely responsible. Now the baton has been passed to legislators and regulators, having proven that the process works and can change corporate behaviour for the better. It's also a fantastic acknowledgement of how security researchers have helped governments understand what good looks like and whilst there are too many to name here, they’re based all over the world and all of them passionately believe in making the world a better, more secure place.
Recent work has focussed on the consumer connected product and IoT space – partly because it has been such an obvious car crash for decades (yes, that’s right decades). This has been compounded by companies seeking to transform themselves and ‘digitise’ by connecting their non-connected products to the internet – at low cost, and without embedding security as a design requirement. Couple this with an increasingly tooled-up set of criminals with lots of different motivations leaves IoT manufacturers exposed to attack.
Vulnerability Disclosure In Legislation And Regulation
There’s a huge amount of cyber security legislation that has been coming through as governments around the world wake up to the reality that their entire economies are dependent on a functioning and safe internet. In the IoT space, the technical standards are all in place, allowing governments to mandate them. The world-leading ETSI EN 303 645 specification covers IoT device security and mandates vulnerability disclosure policies – and more importantly that companies act on them in a timely manner. NIST’s work on IoT security has also been instrumental, especially in response to the US President’s May 2021 Executive Order 14028, ‘Improving the Nation’s Cybersecurity’ which also included vulnerability disclosure and management.
ETSI EN 303 645 has been adopted across the world including Australia, Finland, India, Singapore and Vietnam. Other broadly aligned work exists in Brazil, France, Germany, Japan, Oman, Saudi Arabia and UAE with more to come. The EU’s draft Cyber Resilience Act will put in place a provision that manufacturers must handle vulnerabilities disclosed to them throughout the whole lifecycle. For critical industries they’re already subjected to vulnerability disclosure requirements in the NIS2 Directive. China is heading in a similar direction but the standards and regulations are opaque. The UK passed the Product Security and Telecommunications Infrastructure (PSTI) Act in December 2022 which puts the vulnerability disclosure requirement into law. The country laid out its accompanying regulations banning default passwords, mandating vulnerability disclosure and requiring transparency on minimum software update lifetimes in late April 2023. with the date for compliance set as April 29th 2024, starting the final timer for IoT product manufacturers to get ready.
Company Exposure
So, if this is the direction, why haven’t we seen more action by the manufacturers and companies involved in the IoT sphere? We’ve been conducting our research for the past five years with the same methodology so we’ve been able to track progress. The progression of adoption has been broadly linear, but to the extent that, at the current rate, full adoption of vulnerability disclosure programmes would in theory be in 2039! We had expected to see an acceleration in adoption this year with the various initiatives from governments around the world. What we are perhaps seeing instead, is the exact reason why countries have felt the need to legislate. There is demonstrable market failure that presents a security risk too great to leave to the discretion of company policies that don’t go far enough.
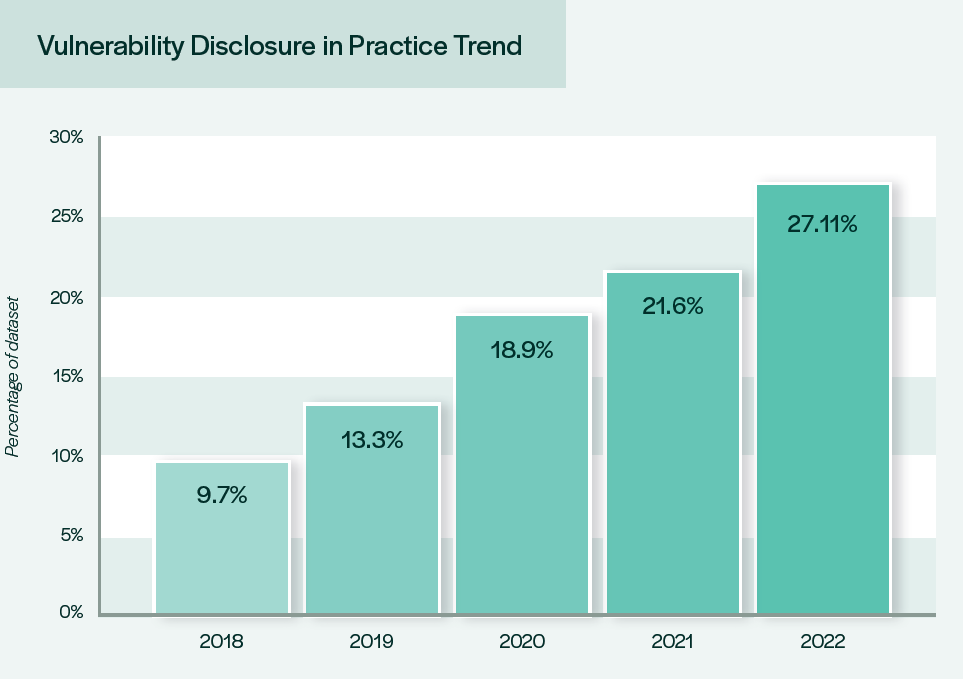
Graph from the fifth annual report into the state of vulnerability disclosure in IoT showing the slow progress of adoption of vulnerability disclosure policies by companies.
What happens next? Well, in countries that are regulating, there’ll be enforcement bodies and reporting mechanisms for non-compliance. In some there’ll be very large fines. Security researchers have another outlet to go to if they’re ignored by IoT manufacturers. Then, maybe then, we’ll see companies start taking vulnerability disclosure seriously.
If you’d like to hear more insights from the State of Vulnerability Disclosure in IoT report and the wider global policy implications, you can watch the on-demand webinar which took place on the 23rd of March 2023. The discussion weighs in on the state of VDP adoption across multiple IoT sectors and geographical regions, international legislation that could spur more rapid adoption, and best practices stemming from vulnerability disclosure programs at global enterprises.
The fifth annual report into the State of Vulnerability Disclosure Policy (VDP) Usage in Global Consumer IoT in 2022 can be downloaded from the IoT Security Foundation.






















