Offensive security testing tailored for your goals
Root out the most elusive vulnerabilities with targeted, time-bound security testing to meet your specified outcomes.
Align your security objectives with the expertise you need
HackerOne Challenge aligns your business with security experts to find the most elusive vulnerabilities and satisfy objectives defined by your team.
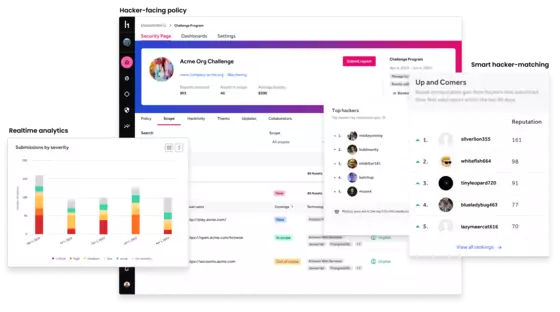
How HackerOne Challenge works
HackerOne Challenge is an invite-only, time-bound offensive testing engagement tapping into the world’s most expansive community of ethical hackers. HackerOne Challenge is curated to meet your individual use case, such as flagging specific vulnerability classes, testing newly released code, or validating security controls already in place.
HackerOne helps determine the scope of digital assets to be tested and helps define the required objective for the Challenge. From there, HackerOne takes point on inviting hackers, conducting tests, triaging results, and producing reports once the Challenge concludes.


Meet security objectives relevant to your business
HackerOne Challenge is a vulnerability-hunting engagement, or time-bound bug bounty, customized to meet your particular security objectives. You determine the duration of the engagement, the assets that are in scope, and the specific skill set you need from the hacker community.
- Align a Challenge with major security initiatives like new releases, or targeted reviews for high-value digital assets.
- Work directly with a HackerOne Engagement Manager to specify the scope and desired outcomes for the Challenge.
- Set the time frame for custom-tailored security testing—including 15-, 30-, or 60-day Challenges.

Readily available skill sets for a broad digital landscape
HackerOne’s global ethical hacking community has the expertise and ingenuity to analyze digital assets, including web, cloud, mobile, IoT, and more. Offensive testing from security experts yields results that are not possible with automation alone.
- Invite ethical hackers to participate in a private Challenge based on your required skill set.
- Select ID-verified and background-checked ethical hackers to analyze sensitive internal assets.
- Communicate directly with HackerOne customer success for effective engagement management.

Tangible vulnerability feedback for faster remediation
HackerOne Challenge delivers comprehensive vulnerability reports to ensure critical vulnerabilities are remediated quickly. Challenge reports include an executive summary, a methodology section, and a detailed account of the vulnerability findings.
- All vulnerability findings are reported within the HackerOne platform as well as in a consumable PDF for compliance needs.
- Feed vulnerability data into your existing bug-tracking tools, including JIRA and GitHub.
- Validate bug fixes by coordinating retests with the original testers.
Internally, we are faster at fixing a HackerOne finding than a finding from anywhere else. We also get nearly zero false positives from HackerOne, thanks to triage. This speaks to the findings' quality and our confidence in HackerOne.
Want to learn more about how HackerOne Challenge can be tailored to meet your needs?
Tell us about your security objectives and one of our experts will contact you.
HackerOne Challenge Solution Brief
While automated scanning tools can help find obvious security flaws within applications, it is preemptive, offensive security testing powered by human ingenuity that can detect the most elusive vulnerabilities.
Zebra Defends Its Attack Surface from All Angles
Learn how Zebra uses vulnerability data provided by HackerOne to strengthen their security program.

HackerOne Challenge Security Assessment
See how you can share vulnerability findings with your team and regulators.